Hi,
This can actually be easily achieved on the current 4.8 firmware; you just need to set the correct mark for the VPN instance.
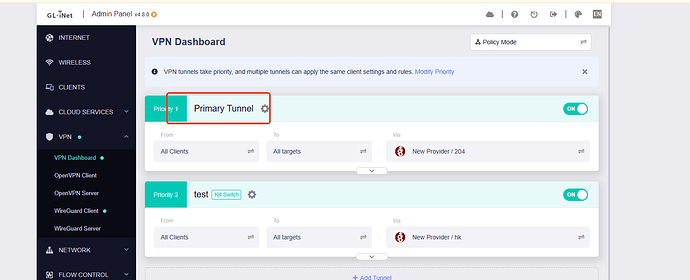
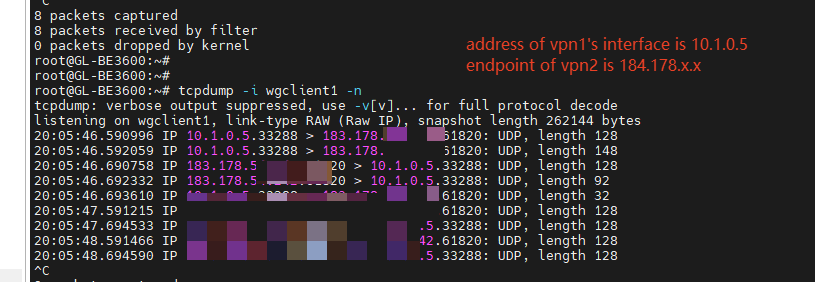
In my test environment, data going through VPN2 will pass through the exit point of VPN1 and then jump to its exit point.
-
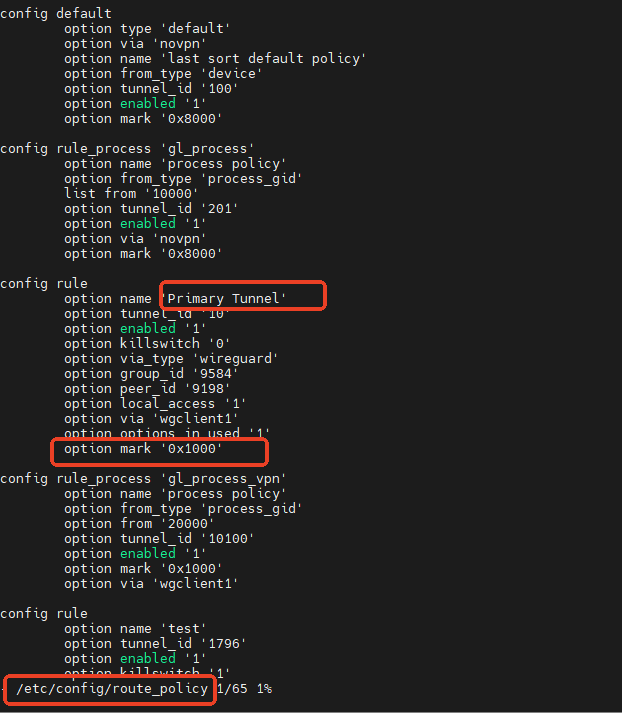
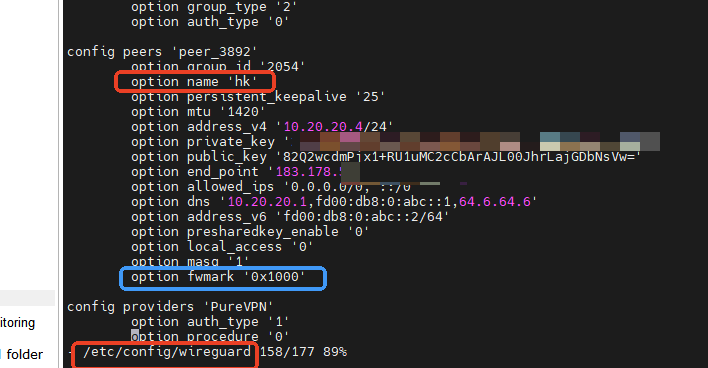
By querying the backend data, you can find out the mark of VPN1's traffic.
-
Simply set the fwmark correctly in the VPN2 tunnel configuration and then reopen VPN2.
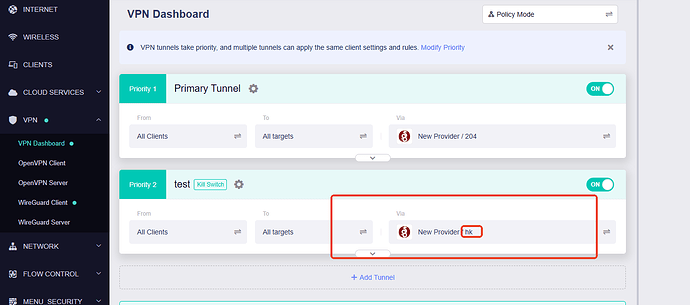
As you can see, communication with the VPN2 server is via the VPN1 tunnel.
After completing the setup, restart the tunnel which using VPN2 as the exit to apply the configuration.
Hope this helps you.