When is it expected that the 4.8 beta Will be released as a stable version?
Hi,
The v4.8 firmware will remain in beta version for testing in a while.
At present, there may be some changes in the GUI. We may release multiple beta version firmware during these months.
I assume (not sure) in the end of Q3 may be the v4.8 converted to stable.
Well, as of 11 it's in RC, I was more attracted to op24 but an RC has to be looked at and in the notes it said just what I was freaking out about: not only a serious vpn policy, but even multi instance and, testing it, incredible wireguard speed.
I liked the novelty so much, I rebuilt the shut them all down button, iterating in a for /etc/gl-sw*d/vpn.sh between a total client start or stop.
And here comes the niptick bug, you forgot in line 19 the novpn via_type. So if like me you use it instead of a configuration, to put the whitelist at the top of the priority instead of in the queue wasting milliseconds and resources, serious if you use it for netflix and google, leaving the vpn to the garbage. In this case it is not turned off by the script and, turned off the other tunnels, it takes up resources unnecessarily.
Any chance to get an op24 version for testing?
Hi, I had this weird incident on the Slate AX (GL-AXT1800) where I would get a bunch of kernel panics when a device attempts to join WiFi:
Oops#1 Part1
<4>[ 211.191200] nf_reject_ipv4 nf_nat_tftp nf_nat_snmp_basic nf_nat_pptp nf_nat_irc nf_nat_h323 nf_nat_amanda nf_log_ipv6 nf_log_ipv4 nf_log_common nf_flow_table nf_conntrack_tftp nf_conntrack_snmp nf_conntrack_pptp nf_conntrack_netlink nf_conntrack_irc nf_conntrack_h323 nf_conntrack_broadcast ts_kmp nf_conntrack_amanda nf_conncount libcrc32c l2tp_ppp iptable_nat iptable_mangle iptable_filter ipheth ip_tables gl_xx crc_ccitt compat cdc_wdm cdc_acm arptable_filter arpt_mangle arp_tables dwc3 dwc3_qcom fuse sch_tbf sch_ingress sch_htb sch_hfsc em_u32 cls_u32 cls_route cls_matchall cls_fw cls_flow cls_basic act_skbedit act_mirred act_gact pwm_fan hwmon qca_nss_wifi_meshmgr xt_set ip_set_list_set ip_set_hash_netportnet ip_set_hash_netport ip_set_hash_netnet ip_set_hash_netiface ip_set_hash_net ip_set_hash_mac ip_set_hash_ipportnet ip_set_hash_ipportip ip_set_hash_ipport ip_set_hash_ipmark ip_set_hash_ipmac ip_set_hash_ip ip_set_bitmap_port ip_set_bitmap_ipmac ip_set_bitmap_ip ip_set nfnetlink
<4>[ 211.261570] ip6table_nat nf_nat nf_conntrack pptp pppox ppp_generic slhc nf_defrag_ipv4 ip6t_NPT ip6table_mangle ip6table_filter ip6_tables ip6t_REJECT x_tables nf_reject_ipv6 bonding ip_gre gre ifb nat46 nf_defrag_ipv6 qca_nss_drv l2tp_netlink l2tp_core qca_nss_dp udp_diag tcp_diag raw_diag inet_diag veth tun qca_ssdk dns_mark ntfs nls_utf8 nls_iso8859_1 nls_cp437 vxlan mtdoops uas usb_storage gl_fan_driver bootconfig xhci_plat_hcd xhci_pci xhci_hcd sd_mod scsi_mod kmwan gpio_button_hotplug gl_sdk4_tertf gl_repeater gl_sdk4_black_white_list vfat fat exfat(C) udc_core usbcore nls_base usb_common mii gl_sdk4_hw_info
<4>[ 211.403241] CPU: 0 PID: 5 Comm: kworker/0:0 Tainted: G C 5.4.164 #0
<4>[ 211.425475] Hardware name: GL Technologies, Inc. AXT1800 (DT)
<4>[ 211.433122] Workqueue: rproc_wq rproc_crash_handler_work
<4>[ 211.438927] pstate: 60400005 (nZCv daif +PAN -UAO)
<4>[ 211.444329] pc : ath11k_core_ssr_notifier_cb+0xd8/0x120 [ath11k]
<4>[ 211.448919] lr : ath11k_core_ssr_notifier_cb+0xc8/0x120 [ath11k]
<4>[ 211.455072] sp : ffffff801e87bc40
<4>[ 211.461056] x29: ffffff801e87bc40 x28: ffffff801ff5e1f0
<4>[ 211.464272] x27: 00000000fffffef7 x26: ffffff801ff5e1a0
<4>[ 211.469654] x25: ffffff801df033c8 x24: ffffff801df03428
<4>[ 211.474949] x23: ffffff801eb27800 x22: ffffff801eb2cc10
<4>[ 211.480244] x21: ffffff801eb27800 x20: ffffff8017de0000
<4>[ 211.485541] x19: ffffff8017de0018 x18: 0000000000000005
<4>[ 211.490837] x17: 0000000000000000 x16: 0000000000000000
<4>[ 211.496132] x15: 0000000000000006 x14: 6163202c30207074
<4>[ 211.501427] x13: 20727563202c3039 x12: 31382070685f7061
<4>[ 211.506722] x11: 6572202c30393138 x10: 0000000000000004
<4>[ 211.512015] x9 : 000000000000008b x8 : ffffff801e87b7f0
<4>[ 211.517311] x7 : 0000000000000000 x6 : ffffff801d7cd891
<4>[ 211.522606] x5 : 0000000000000000 x4 : 0000000000000001
<4>[ 211.527900] x3 : ffffff8017d56b80 x2 : ffffffff003f55a0
<4>[ 211.533195] x1 : 0000000000000000 x0 : 0000000000000000
<4>[ 211.538492] Call trace:
<4>[ 211.543801] ath11k_core_ssr_notifier_cb+0xd8/0x120 [ath11k]
<4>[ 211.545964] blocking_notifier_call_chain+0x7c/0xb0
<4>[ 211.551863] rproc_subsys_notify+0x7c/0x8c
<4>[ 211.556464] rproc_trigger_recovery+0x74/0x284
<4>[ 211.560627] rproc_crash_handler_work+0xcc/0xd0
<4>[ 211.565054] process_one_work+0x1b4/0x320
<4>[ 211.569479] worker_thread+0x6c/0x440
<4>[ 211.573644] kthread+0x128/0x154
<4>[ 211.577292] ret_from_fork+0x10/0x24
<0>[ 211.580594] Code: f9400260 91404800 3971c000 35fffb20 (d4210000)
<4>[ 211.584154] ---[ end trace 2bdba8a4a6d26391 ]---
Panic#2 Part1
<4>[ 211.261570] ip6table_nat nf_nat nf_conntrack pptp pppox ppp_generic slhc nf_defrag_ipv4 ip6t_NPT ip6table_mangle ip6table_filter ip6_tables ip6t_REJECT x_tables nf_reject_ipv6 bonding ip_gre gre ifb nat46 nf_defrag_ipv6 qca_nss_drv l2tp_netlink l2tp_core qca_nss_dp udp_diag tcp_diag raw_diag inet_diag veth tun qca_ssdk dns_mark ntfs nls_utf8 nls_iso8859_1 nls_cp437 vxlan mtdoops uas usb_storage gl_fan_driver bootconfig xhci_plat_hcd xhci_pci xhci_hcd sd_mod scsi_mod kmwan gpio_button_hotplug gl_sdk4_tertf gl_repeater gl_sdk4_black_white_list vfat fat exfat(C) udc_core usbcore nls_base usb_common mii gl_sdk4_hw_info
<4>[ 211.403241] CPU: 0 PID: 5 Comm: kworker/0:0 Tainted: G C 5.4.164 #0
<4>[ 211.425475] Hardware name: GL Technologies, Inc. AXT1800 (DT)
<4>[ 211.433122] Workqueue: rproc_wq rproc_crash_handler_work
<4>[ 211.438927] pstate: 60400005 (nZCv daif +PAN -UAO)
<4>[ 211.444329] pc : ath11k_core_ssr_notifier_cb+0xd8/0x120 [ath11k]
<4>[ 211.448919] lr : ath11k_core_ssr_notifier_cb+0xc8/0x120 [ath11k]
<4>[ 211.455072] sp : ffffff801e87bc40
<4>[ 211.461056] x29: ffffff801e87bc40 x28: ffffff801ff5e1f0
<4>[ 211.464272] x27: 00000000fffffef7 x26: ffffff801ff5e1a0
<4>[ 211.469654] x25: ffffff801df033c8 x24: ffffff801df03428
<4>[ 211.474949] x23: ffffff801eb27800 x22: ffffff801eb2cc10
<4>[ 211.480244] x21: ffffff801eb27800 x20: ffffff8017de0000
<4>[ 211.485541] x19: ffffff8017de0018 x18: 0000000000000005
<4>[ 211.490837] x17: 0000000000000000 x16: 0000000000000000
<4>[ 211.496132] x15: 0000000000000006 x14: 6163202c30207074
<4>[ 211.501427] x13: 20727563202c3039 x12: 31382070685f7061
<4>[ 211.506722] x11: 6572202c30393138 x10: 0000000000000004
<4>[ 211.512015] x9 : 000000000000008b x8 : ffffff801e87b7f0
<4>[ 211.517311] x7 : 0000000000000000 x6 : ffffff801d7cd891
<4>[ 211.522606] x5 : 0000000000000000 x4 : 0000000000000001
<4>[ 211.527900] x3 : ffffff8017d56b80 x2 : ffffffff003f55a0
<4>[ 211.533195] x1 : 0000000000000000 x0 : 0000000000000000
<4>[ 211.538492] Call trace:
<4>[ 211.543801] ath11k_core_ssr_notifier_cb+0xd8/0x120 [ath11k]
<4>[ 211.545964] blocking_notifier_call_chain+0x7c/0xb0
<4>[ 211.551863] rproc_subsys_notify+0x7c/0x8c
<4>[ 211.556464] rproc_trigger_recovery+0x74/0x284
<4>[ 211.560627] rproc_crash_handler_work+0xcc/0xd0
<4>[ 211.565054] process_one_work+0x1b4/0x320
<4>[ 211.569479] worker_thread+0x6c/0x440
<4>[ 211.573644] kthread+0x128/0x154
<4>[ 211.577292] ret_from_fork+0x10/0x24
<0>[ 211.580594] Code: f9400260 91404800 3971c000 35fffb20 (d4210000)
<4>[ 211.584154] ---[ end trace 2bdba8a4a6d26391 ]---
<0>[ 211.599292] Kernel panic - not syncing: Fatal exception
<2>[ 211.599314] SMP: stopping secondary CPUs
<6>[ 211.603324] smem desc phys addr(0x4aa3b198) going to be ioremapped
<6>[ 211.607492] smem_panic_handler tx tail:1704 tx head:1720 rx tail:1784 rx head:1784
<0>[ 216.613723] The reading for sensor 4 is 0x002042b0
<0>[ 216.613745] The reading for sensor 5 is 0x002052b4
<0>[ 216.617395] The reading for sensor 7 is 0x002072a3
<0>[ 216.622169] The reading for sensor 8 is 0x002082a7
<0>[ 216.626944] The reading for sensor 13 is 0x0020d2b4
<0>[ 216.631718] The reading for sensor 14 is 0x0020e2b0
<0>[ 216.636540] Couldn't get reading for sensor 15
<0>[ 216.641350] Kernel Offset: disabled
<0>[ 216.645863] CPU features: 0x0002,20002000
<0>[ 216.649248] Memory Limit: none
This happened occasionally on beta 7 and every few minutes on beta 8.
On beta 8, I also was getting protocol 86dd is buggy errors in the System Log tab.
Both errors were resolved by a wipe / reset, so perhaps it was caused by some configuration I am unaware of.
@scsh If you're on beta 8, I'd try the RC before worrying, it was released on July 11.
@gl.support I'd like to know where the VPN server/client cascading has gone. The firewall seems OK, the server sees the LAN but not the WGC. I'm using the multi-instance client, I'd like the server to be seen as any internal device. As it was before, I don't think multi-instancing makes it much more complicated, maybe it's just an oversight in the GUI modification (it was set from the server in the dashboard, which has been removed).
What is the v4.8 version of OpenWrt based on? Is it OpenWrt 23.05?
OpenWrt 21.02-SNAPSHOT
I tried the latest 4.8.0 beta on my MT-3000 yesterday, but I needed to revert to 4.7.x since AdGuardHome needs to reach DNS Server which are behind the VPN, but since 4.8.0 AdGuardHome seems to be unable to connect to DNS servers behind the VPN. Clients behind the VPN can reach them.
It's still 21.02? that sucks, I guess i'm staying in 4.7
Gutted there is no option for the Flint3 yet. The new interface on the Flint2 for the VPN dashboard is great. Received the Flint3 and back to the old Interface ![]()
Flint3 is being adapted. I hope to publish the beta next week.
You're a star. Thank you ![]()
The op24-v4.8.0 firmware for Flint 2 and Beryl AX are coming soon, based on op24.10.2 (if ready), I hope it meet us within 2 weeks.
Hello,
If enable "AdGuard Home Handle Client Requests", all client DNS will hand by ADG.
It changes the configure method:
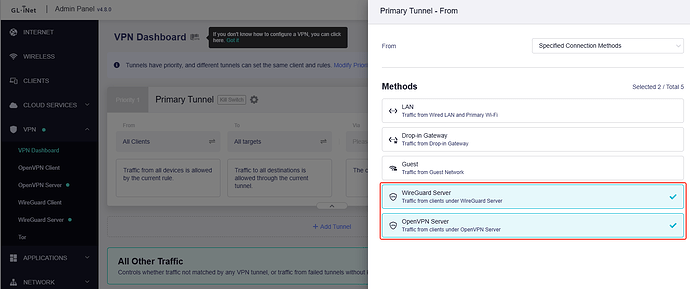
tick the WG server or OVPN server, that will let the traffic from server and go to client
Yes, but the upstream dns server adguardhome should use, can only be reach via vpn, which does not work with v4.8.0
@bruce You're in for a flood of surprises. Yesterday, I was about to activate Adguard, but then I checked the DNS and found DOH on the table, so I no longer need Adguardhome, just their DNS. @Zoey
Edit: Do you know what would be really useful? A ping in ms on failover, so if it's online but slow, it switches to the backup. Now you'll tell me that it already exists!
4.8.0 beta 8 is based on OpenWRT 23.05 for the Slate AX 1800
It appears wireguard is broken on this update, I see these RPC calls that just keep retrying
root@GL-MT3000:/usr# tail /var/log/nginx/error.log
2025/07/19 09:31:31 [notice] 10994#0: *2131 [lua] rpc.lua:263: call(): call: 'wg_client.gen_key', client: 192.168.8.105, server: , request: "POST /rpc HTTP/1.1", host: "berylax.wg.goodkind.io", referrer: "https://berylax.wg.goodkind.io/"
2025/07/19 09:36:02 [notice] 10993#0: *2338 [lua] rpc.lua:263: call(): call: 'wg_client.gen_key', client: 192.168.8.105, server: , request: "POST /rpc HTTP/1.1", host: "berylax.wg.goodkind.io", referrer: "https://berylax.wg.goodkind.io/"
2025/07/19 09:36:07 [notice] 10993#0: *2338 [lua] rpc.lua:263: call(): call: 'wg-client.set_config', client: 192.168.8.105, server: , request: "POST /rpc HTTP/1.1", host: "berylax.wg.goodkind.io", referrer: "https://berylax.wg.goodkind.io/"
2025/07/19 09:36:14 [notice] 10993#0: *2357 [lua] rpc.lua:263: call(): call: 'vpn-client.set_tunnel', client: 192.168.8.105, server: , request: "POST /rpc HTTP/1.1", host: "berylax.wg.goodkind.io", referrer: "https://berylax.wg.goodkind.io/"
2025/07/19 09:36:23 [notice] 10994#0: *2400 [lua] rpc.lua:263: call(): call: 'wg_client.gen_key', client: 192.168.8.105, server: , request: "POST /rpc HTTP/1.1", host: "berylax.wg.goodkind.io", referrer: "https://berylax.wg.goodkind.io/"
2025/07/19 09:36:23 [notice] 10994#0: *2398 [lua] rpc.lua:263: call(): call: 'wg_client.gen_key', client: 192.168.8.105, server: , request: "POST /rpc HTTP/1.1", host: "berylax.wg.goodkind.io", referrer: "https://berylax.wg.goodkind.io/"
2025/07/19 09:49:29 [error] 10993#0: *2425 [lua] oui-ws.lua:91: failed to receive a frame: failed to receive the first 2 bytes: closed, client: 192.168.8.105, server: , request: "GET /ws?sid=LVzqs1RnGMLeJ8fjVwBcaKwnHCizDKWp HTTP/1.1", host: "berylax.wg.goodkind.io"
2025/07/19 09:49:29 [error] 10993#0: *2425 attempt to set status 500 via ngx.exit after sending out the response status 101, client: 192.168.8.105, server: , request: "GET /ws?sid=LVzqs1RnGMLeJ8fjVwBcaKwnHCizDKWp HTTP/1.1", host: "berylax.wg.goodkind.io"
2025/07/19 09:59:49 [notice] 10993#0: *3091 [lua] rpc.lua:263: call(): call: 'wg_client.gen_key', client: 192.168.8.105, server: , request: "POST /rpc HTTP/1.1", host: "berylax.wg.goodkind.io", referrer: "https://berylax.wg.goodkind.io/"
2025/07/19 10:09:14 [notice] 10993#0: *3893 [lua] rpc.lua:263: call(): call: 'vpn-client.stop', client: 192.168.8.105, server: , request: "POST /rpc HTTP/1.1", host: "berylax.wg.goodkind.io", referrer: "https://berylax.wg.goodkind.io/"
This exact configuration worked flawlessly before the update