I have a GL-AX1800 Flint, and I bought it to run a Wireguard server on it.
But my ISP asks 10$ per month for a public IPv4, so I was wondering if I could run it on IPv6 instead.
My ISP also forces me to use their router, so the GL-AX1800 is behind their router.
I have tried AstroRelay and it worked first time, but because I will be using the VPN for remote access the whole day, this will be even more expensive.
I am no networking expert by any means, so I am wondering if IPv6 is a workable solution, and if anyone has it working for them. I am not too worried about leaks, I am not doing anything particularly secret.
Thanks for any help
I haven't as leaks are unacceptable to my use case... but here's something to consider towards your overall goal:
I haven't used it but it would seem to be just the thing for your scenario.
You shouldn't need much more skills than editing a text file. See the following for a primer & a good habit to get into:
Then see the following thread:
Thanks a lot for all this info.
I wanted to start with the good habit and script the list of installed packages.
However, I am already stuck at “copy or upload the script to an easy to remember location/dir”
Do you mind showing me how to upload a file ?
I read the rest of the article and once passed that I am confident that I can do all the other steps, but I couldn’t find how to upload a file to the directory in the router. I do have the OpenWRT session open in PuTTY, and creating the directory was easy.
Even in the OpenWRT Wiki I couldn’t find how to upload a file.
(I did figure which packages are installed by looking at what the script does, I am just stumbling on the upload part, I got arc.list and lbstdcpp6.list on my router)
That’s where openssh-sftp-server comes into play; install it as it’s not apart of the stock GL version of OpenWrt. opkg update && opkg install $packageNameHere. FileZilla is an excellent, free SFTP client application to graphically up/download files to/from the GL device. There are other SFTP applications but YMMV, of course. See the References & Resources links in that same thread.
You need to make a directory before uploading the script to it; the command to mkdir is given.
I did it successfully with the Opal behind my ISP ONT, you just have to change some stuff on the wireguard config that the router creates for your device:
The endpoint to [Your glinet router IPv6]:51820
MTU: 1320 otherwise you’ll lose packages
And I personally used Adguard as DNS servers (94.140.14.14)
It works like charm, don’t forget to assign a static public (28…) IPv6 for your router from the ONT and enable DMZ for it. That’s pretty much it.
Good luck
Attached picture of config file
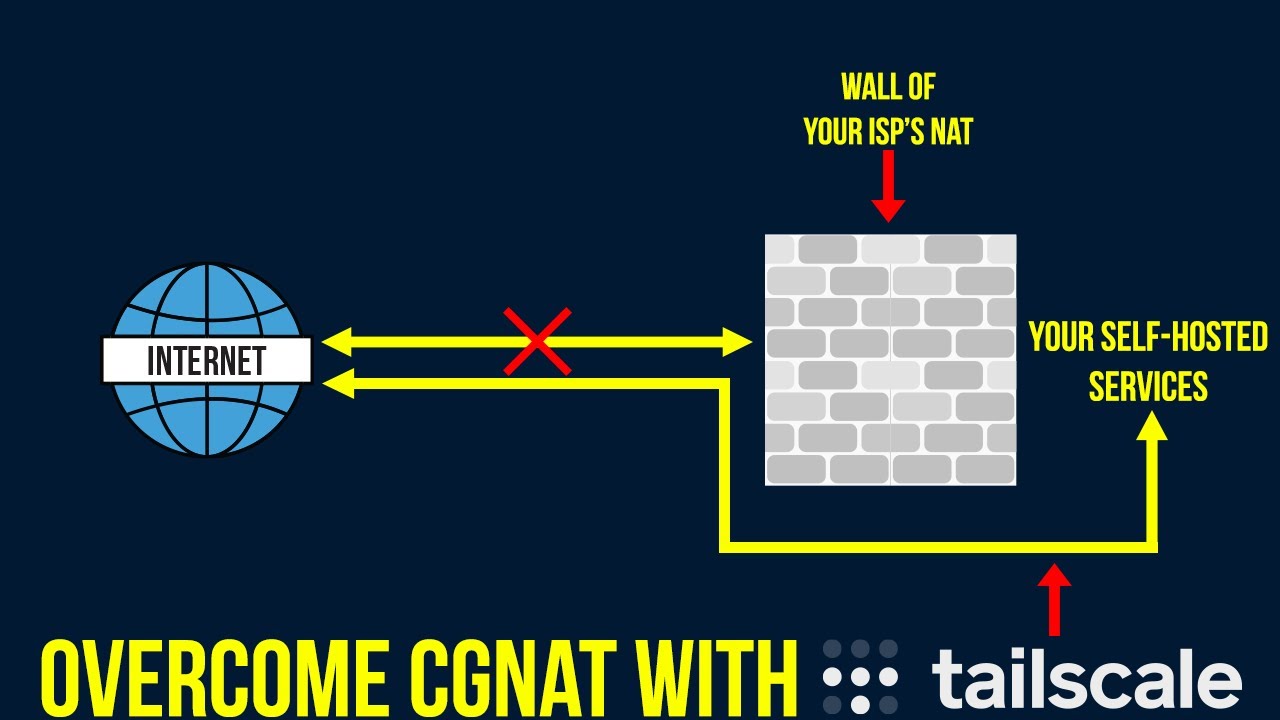
I’ve overcome CGNAT with CloudFlare Tunnels, and a $2 domain name. Plex streams flawlessly, and access my home network no issues, with the added security of ZeroTrust
Thanks a lot for your help, I want to try the same as you did, but I am stumbling on the following:
don’t forget to assign a static public (28…) IPv6 for your router from the ONT I looked into the router config, and I can only do IP reservation for IPv4 addresses, and not for IPv6.
I still want to try setting up the config file of Wireguard as you suggest, and I am trying to figure the IPv6 of my GLinet router, but there are many to choose from, I don’t know which one to pick:
And then even more if I look at my ISP’s router:

Another confusing thing is that when I go to whatismyip.com, I see my IPv4, but it says that I don’t have an IPv6
What do you reckon?
UPDATE: I have tried the first IPv6 above, the one that I erased with the blue color. When I tried to enter it like this with the /64 at the end and inside square brackets, the Wireguard app complained about the format. Then I entered it without the /64, I got no complaint about the format any more, but the VPN client doesn’t connect with the VPN server.
Thanks for that, it is clear now.
So I tried Tailscale, and I was able to set it up without problems, on my phone and on the Flint router. All looks good in the Tailscale control panel, both devices are connected and green.
However, when I decide to set the router as an exit point, then it doesn’t work, the apps on my phone lose the connection to the Internet.
If I don’t set the router as an exit point, then whatismyip.com still shows the same IP as when I am not using Tailscale, so it looks like my phone’s traffic isn’t using Tailscale at all in that case.
Do you have an idea what could be wrong?
Did you hard code your tailnet details into that script mentioned in my first post ITT?
I didn’t originally because I thought the topic was about how to keep the config after a reboot of the server, and I am at the point of trying to get it to work, so the restart issue will come later.
But now I have tried the setting that is mentioned at the top of that topic, about advertising the exit node. I didn’t understand the other options, about routes, they look specific his network.
So here is what I have done:
I get some error messages, Tailscale is up on phone and router, but same behavior as before.
I see… the major difference it appears is your need for Ethernet’s IP Address (IPv6) & how that’s used within the tailscale up command string. Once you’ve got your tailnet up manually, it should just be a matter of editing the aforementioned script to have it come up on next boot.
… but I don’t use Tailscale nor IPv6 so I’m no good to you from here.
What seems to be happening here is that your ISP provides your ONT with an IPv6 but that router isn’t assigning IPv6 to your connected devices, check if there’s an option to enable the DHCPv6 server on it, you must be looking for something like this
Once your ISP router starts assigning IPv6 to the devices, the IPv6 address assigned to your GliNet must appear in your GliNet router on the internet section like this:
I hope you can find the DHCPv6 option, maybe it’s named differently in your ISP router, depending on the model try to search for the equivalence on it.
Use this https://test-ipv6.com/ to check if you’re being assigned an IPv6 address
And yes the IPv6 must finish with /64 which you must not include in the endpoint, just until :XXXX] and that’s it
I have version 4.1.0 of the GLinet admin panel, and yes it looks a bit different from your screenshot: I don’t have a separate tab for IPv6, I have both on the same tab, it corresponds to my screenshot above where I have hidden the addresses in green color.
Anyway, I checked the test site you provided, and indeed my ISP isn’t assigning me an IPv6, so I have created a ticket with them, let’s see how it goes…
Also thank you for the info on the format of the IPv6, it is one of those little things that blocks you for hours otherwise )
Thank you for this suggestion, I wasn’t aware that this was an option. I went to the Cloudflare site looking for more info, but they are always pointing me to corporate solutions. I read their white paper about remote access, but it didn’t click.
What I need is that not matter where I am, I can route my web traffic through my router at home, so that all web sites keep on seeing my home’s IP address.
I imagine there is a way to achieve this with Cloudflare, I just haven’t found it yet. Do you have link where this is described?
I also found this Building a Pet Cam using a Raspberry Pi, Cloudflare Tunnels and Teams but how do I adapt it to run on GLinet instead of Pi, and how do I tell the router what to do with the traffic that will be coming from the tunnel?
If you’re looking @ Cloudflare Tunnels on GL, I’d suggest splitting this off into a new thread. If only to keep things more cleanly organized for yourself & responders, I’m also sure the question will be raised by others facing the same concern in the future.
You can always link back to anything specifically referred to as posts ITT.
That’s just my 0.02USD, of course.
That makes sense. It is not clear yet that Tunnels can be a solution for what I am trying to do, namely use my home router as an exit node of all my traffic. If feedback comes showing that Tunnels can be an alternative, I’ll open a new thread because this will be very interesting.