Hi,
I have a GL-AXT1800 with 4.8.2 release 5 up and running.
I would like to use this device as a wireguard VPN-bridge to a company LAN.
However I’m running into the problem, that once I enable policy mode in the VPN Dashboard and limit the flow to the actual IP range that is available behind the VPN, DNS queries don’t go through the tunnel anymore. If I disable policy mode or set it to “all targets” DNS queries are reaching the VPN-Server. My first thought was, that this a routing issue, however the DNS server responds to pings or RDP however no packets on UDP port #53 are sent thru the tunne once manual policy mode is enabled.
I did some snooping around in LuCI and found some #53 DNS-Leak prevention rules for lan and wg . But enable / disabling them didn’t change the behaviour. I found in the forum that recent firmware release made som changes to how DNS behaves and leaks are prevented, so this behaviours might be related to that?
GL-inet LAN: 10.44.101.0/24
wg-local-ip: 10.44.0.101/32
wg-NAT is disabled, both networks are routing fine in both modes!
Remote LAN: 10.10.0.0/16
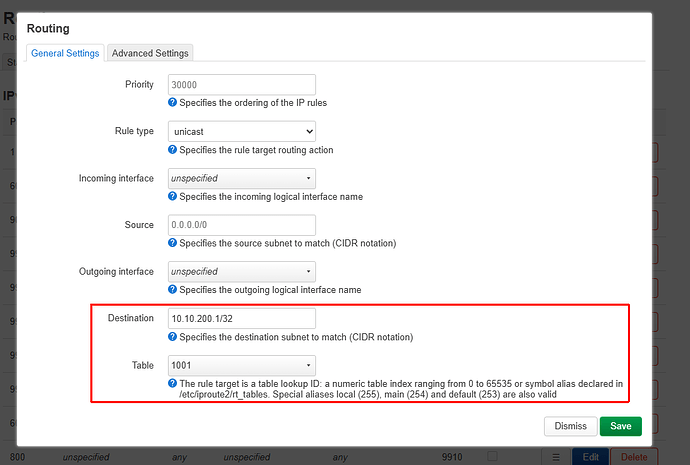
Remote DNS: 10.10.200.1
GL-inet is connecting to WAN via WiFi-DHCP. DHCP IP is 192.168.0.20/24
Thanks,
Dark-Sider
Hi
In ATX1800 v4.8.2, when the VPN is in policy mode, only the domains included in the policy are resolved via the VPN DNS.
All other DNS traffic is routed out through the WAN by default—even if the DNS requests originate from LAN devices and their target DNS server is included in the VPN policy.
We plan to improve this behavior in future versions. Specifically, if a DNS query originates from a LAN device and its destination DNS server is included in the VPN policy, it will be routed through the VPN tunnel.
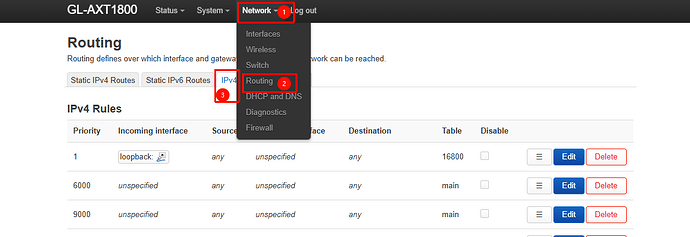
For the current version, you can add a rule under Luci → Network → Routing → IPv4 Rules to force all traffic destined for the VPN DNS server to go through the VPN.
Hi,
thanks for your explanation which solves / explains a different problem with the split-tunnel (policy mode manual) setup. I would have liked that once the VPN is established every DNS query goes to the DNS provided by the VPN connection. I solved this by distrubting that DNS server via DHCP to the clients attached to the AXT1800. While this is not an ideal solution it works for this specific setup.
However the issue I described is a different one. When in manual Policy Mode all DNS queries sent by a CLIENT directly to a Server behind the VPN-tunnel gets dropped by the AXT1800 (as in it never reaches the other router). Pinging the very same IP just works fine, and once I switch to the “all" targets” policy mode DNS requests no longer get dropped and are received by the DNS server behind the tunnel. The AXT1800 internal DNS-server is not used in this setup (see above). Also the AXT1800 also is unable to reach the DNS behind the VPN in the manual policy mode.
However I found this thread MUDIV2 4.8.3 beta issues - #4 by will.qiu basically describing the same issue. So I downloaded the nightly build of the 4.8.3 beta for the AXT1800. After the update (and after switching the policy mode around, so the IP Tables rules get recrated) it immediately started working in manual policy mode.
When comparing the “settings backup” from LuCI the /etc/config/firewall enables the “*_drop_leaked_dns" rules.
I’m glad the latest beta fixes the problem. Now I’m waiting for the stable 4.8.3 release. I’ll also consider your proposed changes to use the AXT1800 DNS server for requests again!
It seems we are describing the same issue: DNS queries specified by LAN devices (whether assigned via DHCP to LAN clients or forwarded by the router by default) are not routed through the VPN when policy mode is enabled.
In any case, we’re glad to hear that you found a way to resolve it.