Hi everyone,
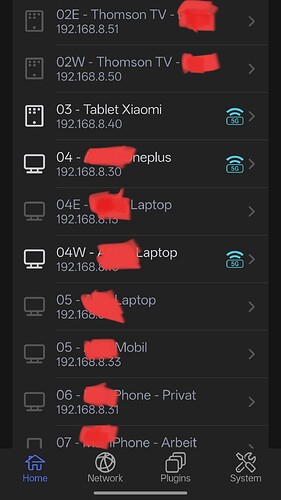
I have two Flint 2 routers running Firmware 4.8.3 in two different locations. For months, they have been working flawlessly with a complex setup: 5 WireGuard client tunnels (NordVPN), Tailscale (advertising subnets), and AdGuard Home (AGH) acting as a Tailscale DNS server for my mobile devices.
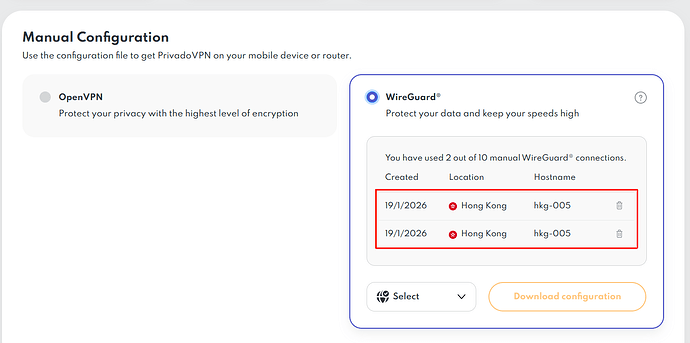
Since my NordVPN subscription was expiring, I decided to switch to ProtonVPN. To my surprise, I am encountering the exact same stability issues I previously had with PrivadoVPN (which I had initially dismissed as a provider-specific problem).
The Problem: When I switch from a NordVPN WireGuard profile to Proton or Privado, my internet and Tailscale connections immediately start dropping. The router becomes inaccessible 90% of the time, with only brief windows of connectivity. The VPN logs are flooded with errors. As soon as I switch back to NordVPN, everything works perfectly again.
What I’ve tried:
-
Adjusting MTU to 1350.
-
Toggling "Force VPN DNS" on/off.
-
Forcing custom Upstream DNS servers in AGH.
-
Testing multiple VPN servers with different configurations.
My observations on DNS behavior:
-
With NordVPN: To use AGH as a remote Tailscale DNS, I had to disable Nord's internal DNS and use encrypted Upstream DNS servers in AGH (ffmuc, uncensoreddns, etc.). This allowed private resolution for home devices and remote Tailscale clients simultaneously.
-
With Proton/Privado: It seems nearly impossible to "bypass" their internal DNS in favor of my encrypted ones. However, unlike Nord, Proton/Privado do seem to allow DNS resolution for remote Tailscale clients.
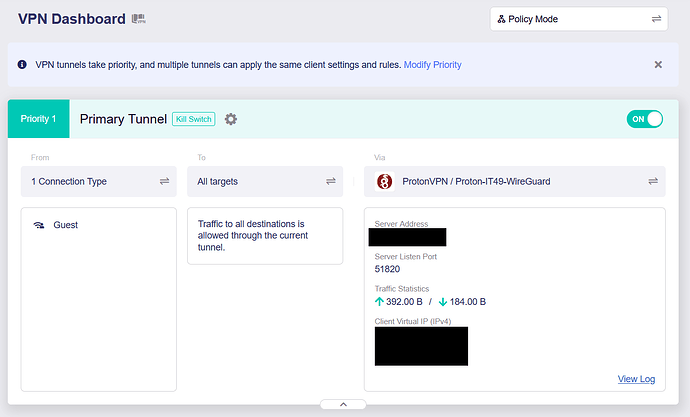
If I disable the Killswitch, set the MTU to 1350, and use the VPN's own DNS servers (instead of my custom encrypted ones in AGH) while performing the switch, stability improves significantly. Curiously, by following these steps, I finally managed to get one of my Flint 2 routers working perfectly with Proton. However, I cannot replicate this success on the second router despite having theoretically identical settings. Now that the first router is finally stable, I am reluctant to touch it and won't be switching back to Nord!
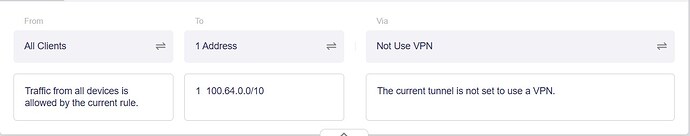
It feels like a routing conflict between how these specific VPN providers handle DNS requests when AGH and Tailscale are active. I was under the impression that Tailscale traffic bypassed the VPN tunnel, but this behavior suggests otherwise.
Has anyone encountered similar conflicts with ProtonVPN on GL.iNet hardware? Any hints on why NordVPN works so differently regarding DNS routing in this ecosystem?
Thanks in advance for your help!