Hello,
As a company focused on network security, GL.iNet is committed to providing users with a more robust underlying architecture.
Beginning with firmware v4.8.3, we have made a major upgrade to the system time synchronization component:
Chrony (chronyd) is now officially introduced as the default time service, replacing the traditional ntp service (sysntpd), which has shown its limitations under modern security standards.
This improvement enhances the security of Internet time synchronization by adding support for the NTS (Network Time Security) protocol, building a stronger defensive barrier for users' network environments.
The NTP component has been deprecated. In response to earlier community discussions about NTP server configuration and redirection requirements, this guide will be updated and adapted based on the Chrony component.
Tutorial:
-
Check whether the router system time is correct
date # If the time is incorrect, you can trigger it manually: /etc/init.d/chronyd restart -
Edit the Chrony configuration to enable the time server, please modify [Router LAN IP] according to your LAN IP
echo "allow [Router LAN IP]" >> /etc/chrony/chrony.conf # For example, allow all clients in the 192.168.8.0/24 subnet to synchronize time from Chrony echo "allow 192.168.8.0/24" >> /etc/chrony/chrony.conf -
Restart Chrony to apply the above new configuration
/etc/init.d/chronyd restart -
Check the port 123 status
netstat -uln | grep 123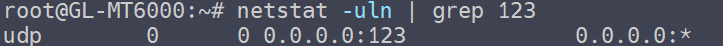
-
Configure the firewall to redirect time requests from LAN clients to the router's time server.
There are two kinds of firewall implementations: some useiptables, others usenft(fw4).
How to tell which is used? Judge with simple/non-rigorous method:cat /etc/os-release | grep "RELEASE"If the OpenWrt version is ≥ 23, then using
nft(fw4); if it is < 23, it generally using iptables.- If your firmware uses
iptables, please modify [Router LAN IP] according to your LAN IP
echo "iptables -t nat -A PREROUTING -i br-lan -p udp --dport 123 -j DNAT --to-destination [Router LAN IP]:123" >> /etc/firewall.user # If your LAN IP range is different, please modify accordingly # For example, redirect the time request from LAN to Router LAN IP, 192.168.8.1 echo "iptables -t nat -A PREROUTING -i br-lan -p udp --dport 123 -j DNAT --to-destination 192.168.8.1:123" >> /etc/firewall.user- If your firmware uses
nftables, please modifydest_ip=according to your LAN IP
uci add firewall redirect uci set firewall.@redirect[-1].name='Redirect-LAN-NTP' uci set firewall.@redirect[-1].src='lan' uci set firewall.@redirect[-1].src_dport='123' uci set firewall.@redirect[-1].dest_port='123' uci set firewall.@redirect[-1].proto='udp' uci set firewall.@redirect[-1].target='DNAT' # Please modify the next line to match your router's LAN IP (default: 192.168.8.1) uci set firewall.@redirect[-1].dest_ip='192.168.8.1' uci commit firewall - If your firmware uses
- Whether using iptables or nftables (fw4), execute after making above changes.
/etc/init.d/firewall restartWhen restarting the firewall you may see print such as "invalid"; as long as they don't mention "error," that's normal.
-
Verify that the redirection is working.
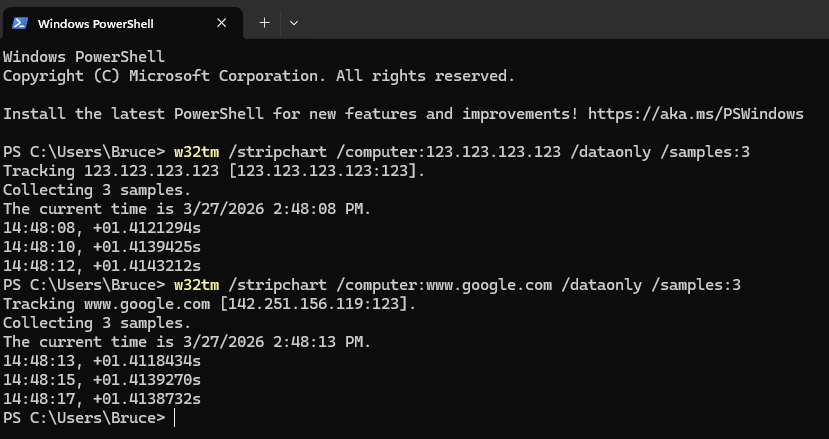
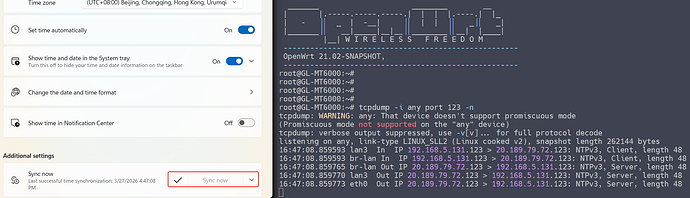
Test using PowerShell on Windows PC on the LAN side. Even if you specify a non-existent IP or Google address, if the result is returned, it means that it is redirected from the router.w32tm /stripchart /computer:123.123.123.123 /dataonly /samples:3 w32tm /stripchart /computer:www.google.com /dataonly /samples:3- Optional: Capture packets using the
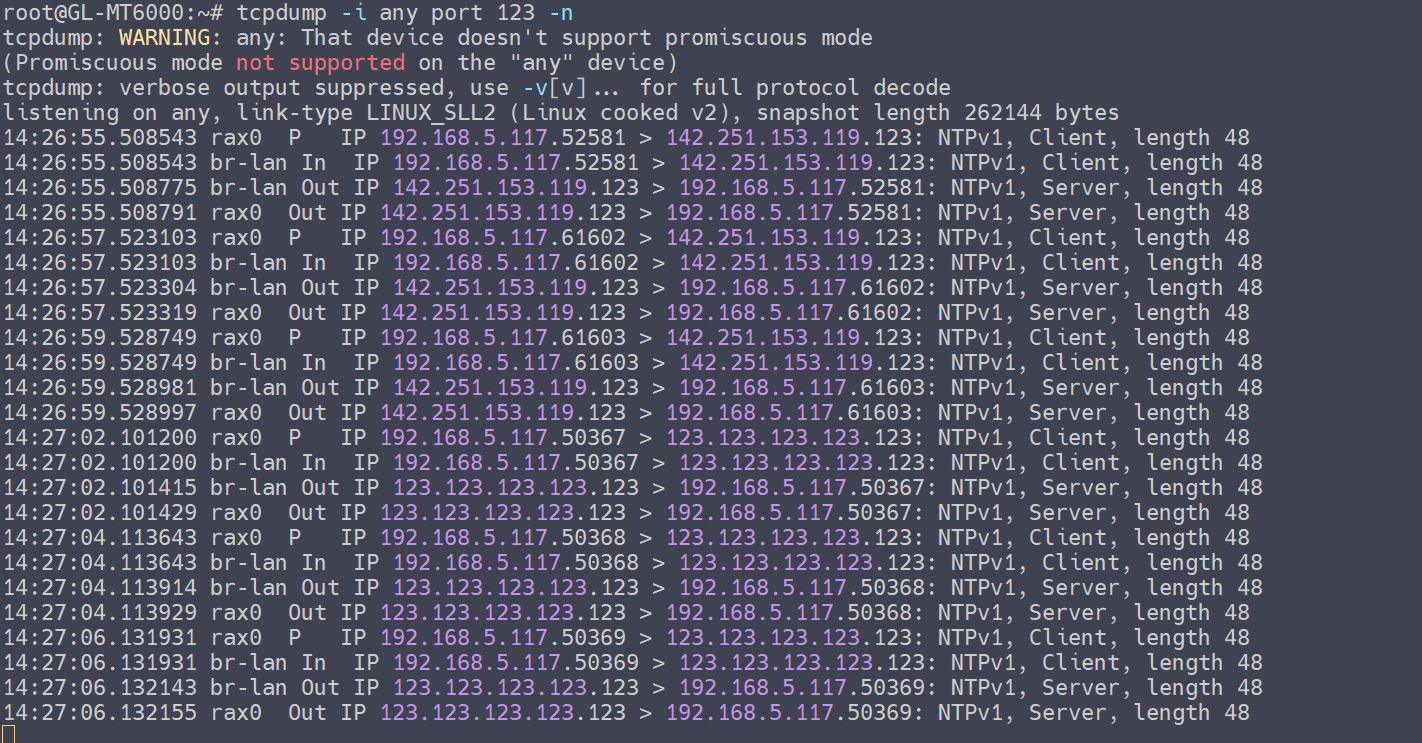
tcpdumpto verify that the LAN client's time requests are being redirected by the router to own host, where time synchronization is provided by Chrony.
opkg update && opkg install tcpdump tcpdump -i any port 123 -n(The router LAN subnet in this example is 192.168.5.0/24, test PC IP is 192.168.5.117)
- Optional: Capture packets using the
-end
Reminder: Please note that all commands involving the [Router LAN IP] must be updated to match your actual IP address. Do not simply copy and paste the commands without replacing the placeholder.