Hello Will,
I have tried that - that didnt work,
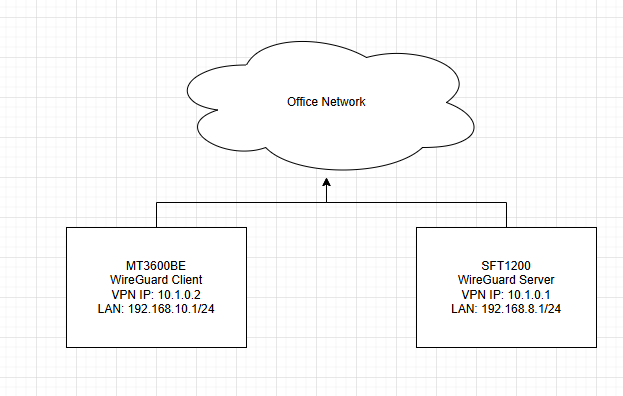
Devices:
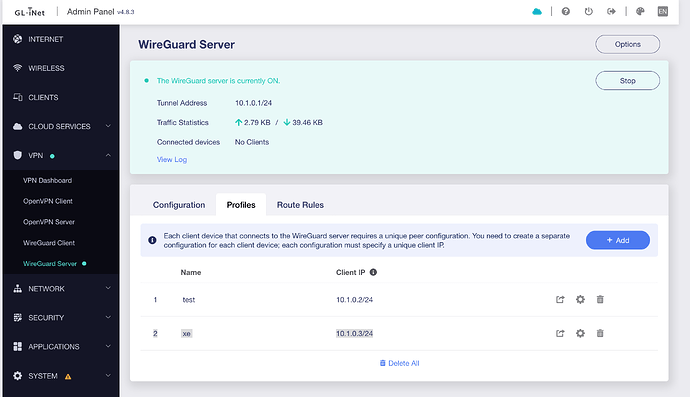
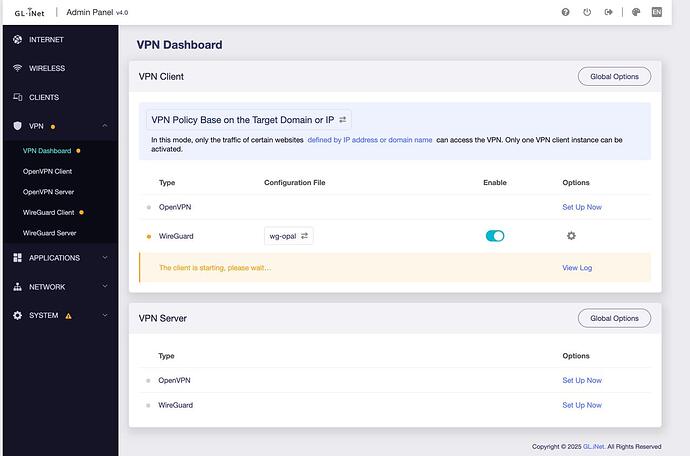
Opal GL-SFT1200 (upgraded to the latest FW), as a wg server [S],
Puli XE300 (fresh fw), as a wg client [C].
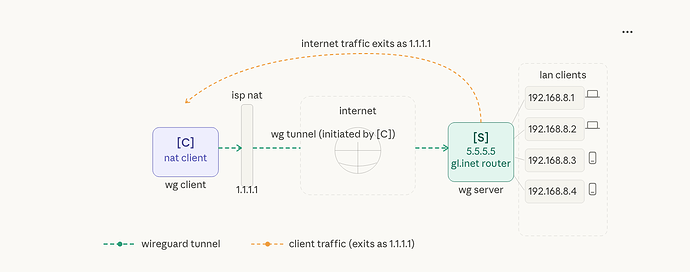
Topology:
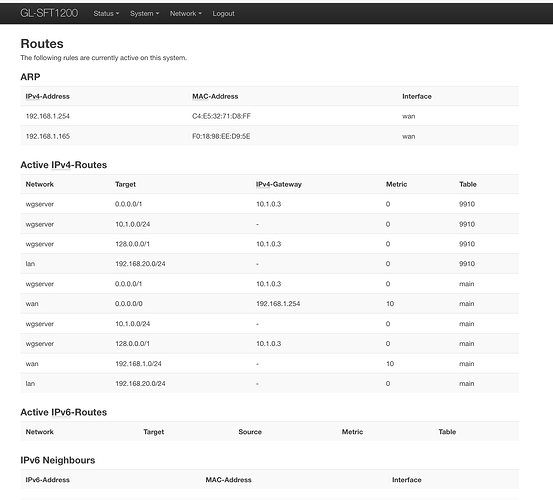
Opal - ext ip: 86.x.x.x:53832 , vpn ip: 10.1.0.1, lan ip: 192.168.20.1
Puli XE300 - uses 4g broadband, vpn ip: 10.1.0.3, lan ip: 192.168.35.1
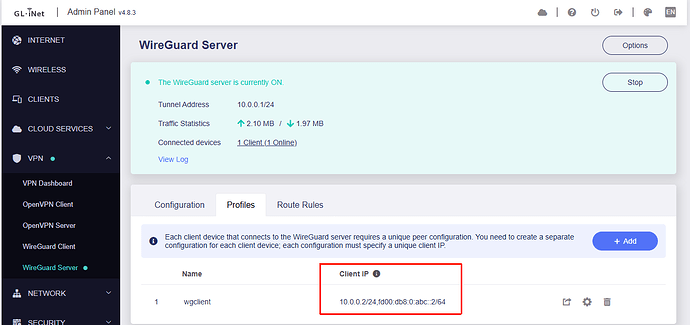
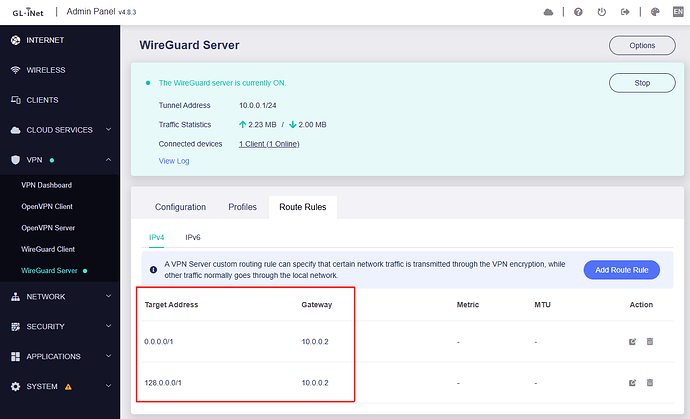
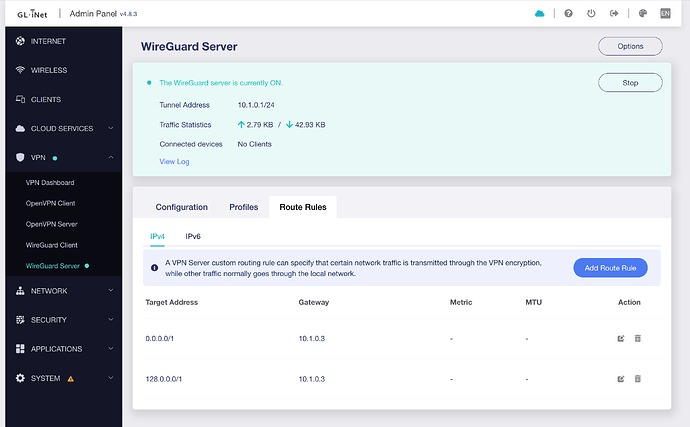
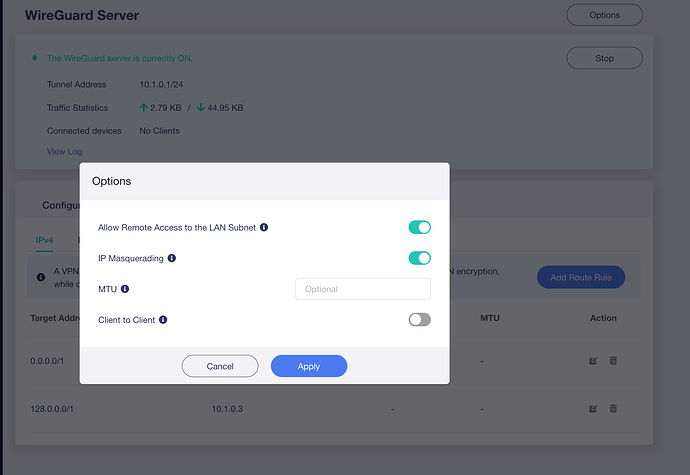
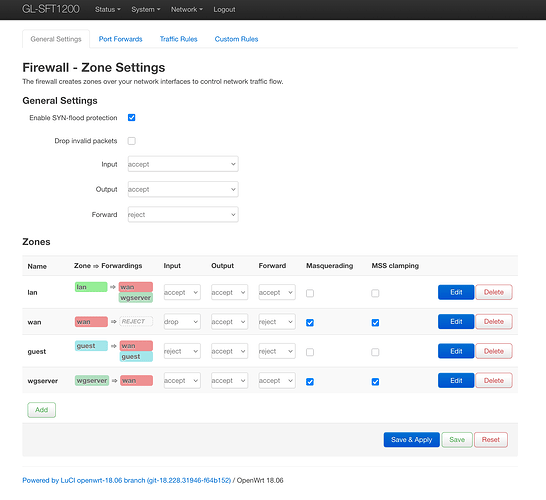
WireGuard Server Configuration [Opal] -
client ip: 10.1.0.3 ,
routing:
(pls dont be confused by some positive statistics in Traffic - that flow was before i applied the route rules)
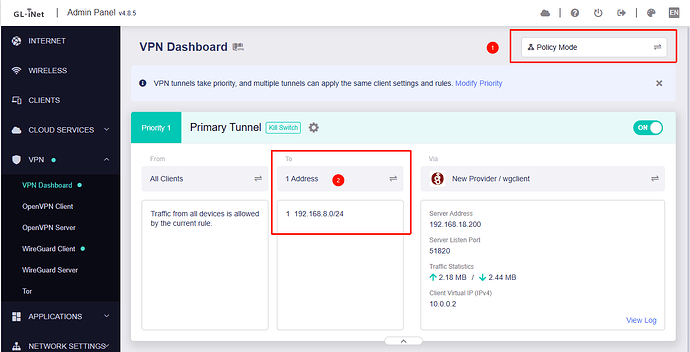
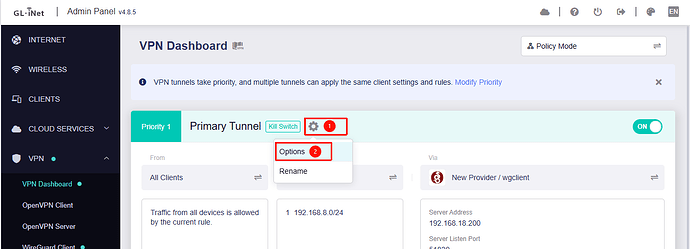
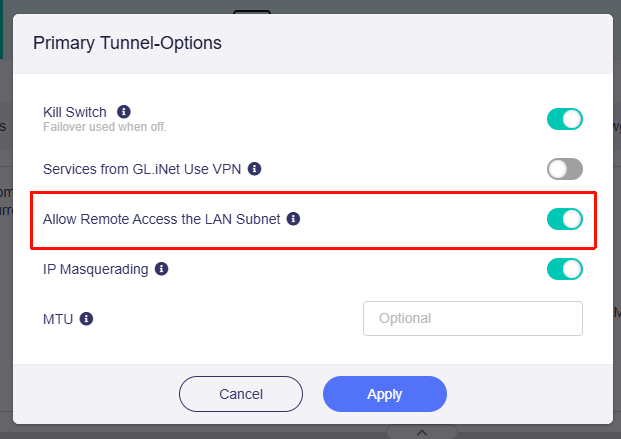
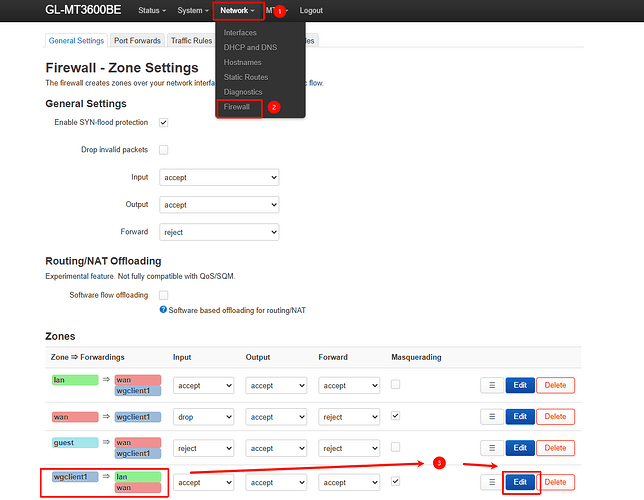
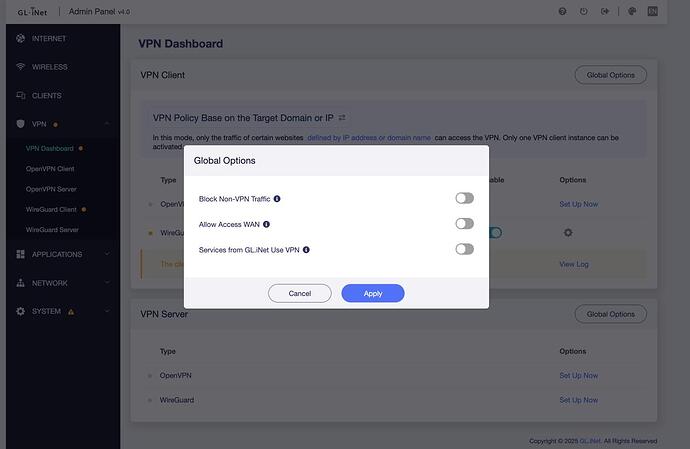
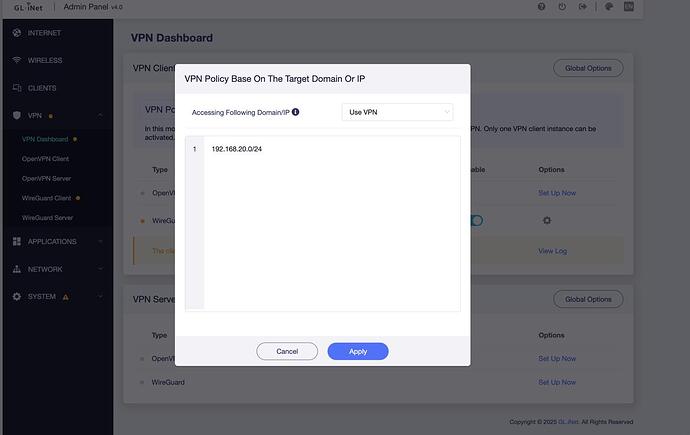
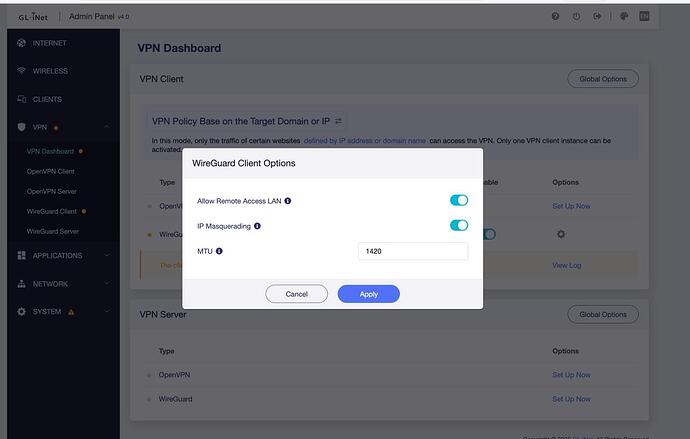
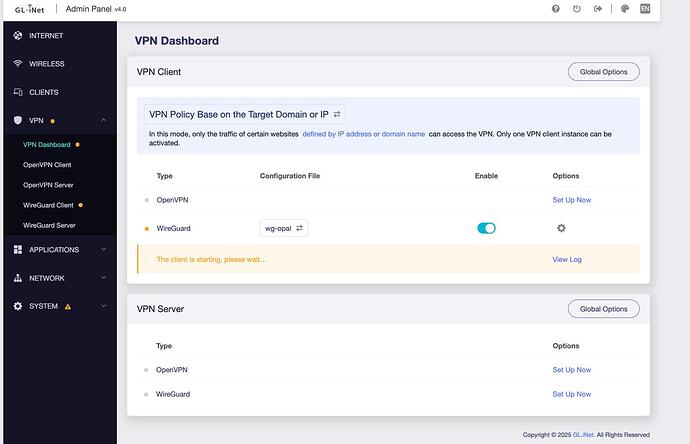
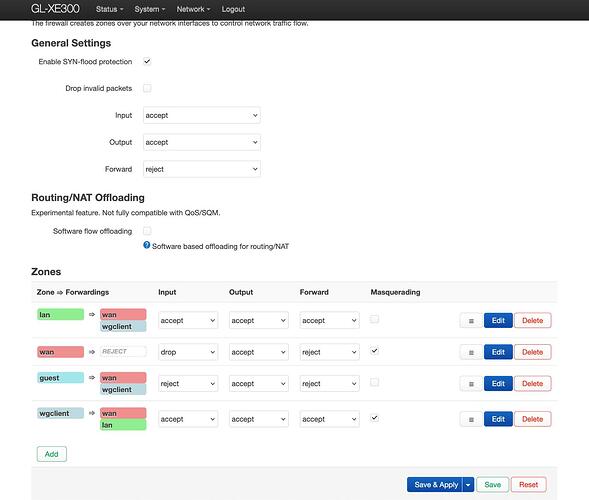
WireGuard Client Configuration [XE300]:
imported configuration, set the policy mode, etc:
The tunnel does not establish on the XE300 side,
here are a few pings from the macbook, connected to Opal via ethernet:
# checking current lan interface
alexs-MacBook-Pro:~ igor$ ifconfig en20
en20: flags=8863<UP,BROADCAST,SMART,RUNNING,SIMPLEX,MULTICAST> mtu 1500
options=400<CHANNEL_IO>
ether 6c:1f:f7:5e:a7:ec
inet6 fe80::d:957a:1b4f:6c29%en20 prefixlen 64 secured scopeid 0x11
inet 192.168.20.147 netmask 0xffffff00 broadcast 192.168.20.255
nd6 options=201<PERFORMNUD,DAD>
media: autoselect (1000baseT <full-duplex>)
status: active
# checking that pings to 8.8.8.8 dont pass
alexs-MacBook-Pro:~ alex$
alexs-MacBook-Pro:~ alex$ traceroute 8.8.8.8
traceroute to 8.8.8.8 (8.8.8.8), 64 hops max, 52 byte packets
1 *
^C
# ping myself
alexs-MacBook-Pro:~ alex$ ping 192.168.20.147
PING 192.168.20.147 (192.168.20.147): 56 data bytes
64 bytes from 192.168.20.147: icmp_seq=0 ttl=64 time=0.107 ms
64 bytes from 192.168.20.147: icmp_seq=1 ttl=64 time=0.085 ms
^C
--- 192.168.20.147 ping statistics ---
2 packets transmitted, 2 packets received, 0.0% packet loss
round-trip min/avg/max/stddev = 0.085/0.096/0.107/0.011 ms
# ping Opal LAN interface
alexs-MacBook-Pro:~ alex$ ping 192.168.20.1
PING 192.168.20.1 (192.168.20.1): 56 data bytes
64 bytes from 192.168.20.1: icmp_seq=0 ttl=64 time=1.035 ms
64 bytes from 192.168.20.1: icmp_seq=1 ttl=64 time=0.921 ms
^C
--- 192.168.20.1 ping statistics ---
2 packets transmitted, 2 packets received, 0.0% packet loss
round-trip min/avg/max/stddev = 0.921/0.978/1.035/0.057 ms
# ping Opal vpn ip
alexs-MacBook-Pro:~ alex$ ping 10.1.0.1
PING 10.1.0.1 (10.1.0.1): 56 data bytes
64 bytes from 10.1.0.1: icmp_seq=0 ttl=64 time=1.039 ms
64 bytes from 10.1.0.1: icmp_seq=1 ttl=64 time=1.035 ms
^C
--- 10.1.0.1 ping statistics ---
2 packets transmitted, 2 packets received, 0.0% packet loss
round-trip min/avg/max/stddev = 1.035/1.037/1.039/0.002 ms
# ping VPN client ip
alexs-MacBook-Pro:~ alex$ ping 10.1.0.3
PING 10.1.0.3 (10.1.0.3): 56 data bytes
Request timeout for icmp_seq 0
Request timeout for icmp_seq 1
Request timeout for icmp_seq 2
^C
--- 10.1.0.3 ping statistics ---
4 packets transmitted, 0 packets received, 100.0% packet loss
alexs-MacBook-Pro:~ alex$
pls let me know if you require more logs, execute any command, etc.
thank you