Dear users:
We've recently become aware that some users using firmware v4.8.0-v4.8.3 have reported needing to enable masquerading of the tailscale zone in the firewall in order for LAN clients able to reach other devices and subnets of their tailnet.
We apologize for any trouble this may have caused.
PHENOMENON:
Even if Tailscale has announced and accepted routes, and approved the subnet in Tailscale cloud console, if masquerading is disable in the tailscale zone of the router's firewall, communication of tailnet can only occur on the router itself, but the router's LAN clients will not be able to access other devices of tailnet (if other devices are also routers, they include the subnets of those routers).
REASON:
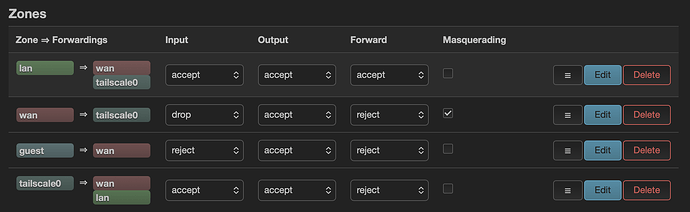
The firmware versions v4.8.0-v4.8.3, we modified the Tailscale firewall rules to improve the security of the router's Tailscale network and ensure more stable tailnet communication. The firewall zone for tailscale appears as follows:
config zone 'tailscale0'
option name 'tailscale0'
option input 'ACCEPT'
option mtu_fix '1'
list device 'tailscale0'
config defaults
option syn_flood '1'
option input 'ACCEPT'
option output 'ACCEPT'
option forward 'REJECT'
The key is to add mtu_fix to ensure large TCP packets are able to pass through correctly, and only LAN clients on the primary (main) network can access the tailnet; but guest clients cannot access to the tailnet or subnets.
Before upgrading to v4.8.0-v4.8.3 firmware, some users had manually added tailscale0 to the WAN zone.
After keep settings and upgrading to v4.8.0-v4.8.3 firmware, Tailscale now has its own dedicated zone, which conflicts with the rules manually added to the WAN zone. Some users have reported that LAN clients are blocked from accessing tailnet, but manually enable masquerade of the tailscale zone (added by firmware) for LAN clients to access normally.
TEMP WORKAROUND:
If you met this this issue in v4.8.0-v4.8.3 firmware,
- SSH to the router and execute the following command to clear the
tailscale0interface in the wan zone:
idx="$(uci -q show firewall | sed -n "s/^firewall\.@zone\[\([0-9]\+\)\]\.name='\?wan'\?$/\1/p" | head -n1)"
[ -n "$idx" ] && uci -q del_list firewall.@zone[$idx].device='tailscale0'
uci commit firewall
/etc/init.d/firewall restart
- If worried that the above is troublesome, you can reset firmware and reconfigure your router.
The expected behavior of the firmware v4.8.0-v4.8.3, does not need to add the tailscale0 interface to the wan zone, nor need to enable masquerading in the dedicated tailscale zone.
Once the Tailscale cloud console has the correct subnet approved, the tailnet communication in LAN clients will work.
SOLUTION:
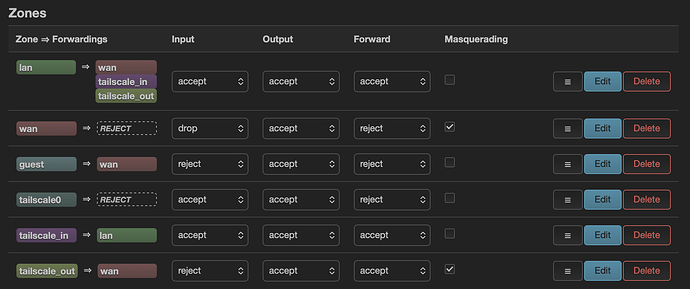
A script will be added in the next firmware update. During the upgrade process, it will check if the user has manually added the tailscale0 interface to the wan zone.
If yes, it will be removed the tailscale0 of wan zone, and the tailscale0 will be assigned to the dedicated Tailscale zone.
This will prevent some conflicts and ensure that users upgrading to v4.8.5 (and later) can use Tailscale without issues, the LAN clients can access other subnets in the tailnet.
-end
We sincerely apologize for the inconvenience this issue may cause!
GL.iNet Technical Support Team