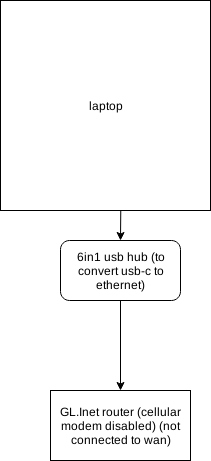
Long story but I've been getting targeted for some reason or another.
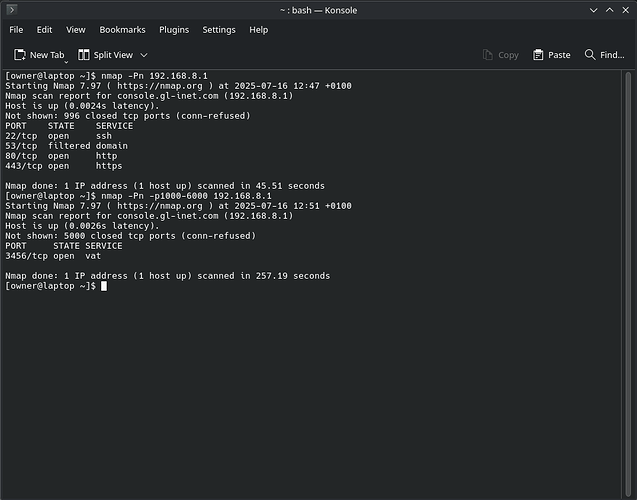
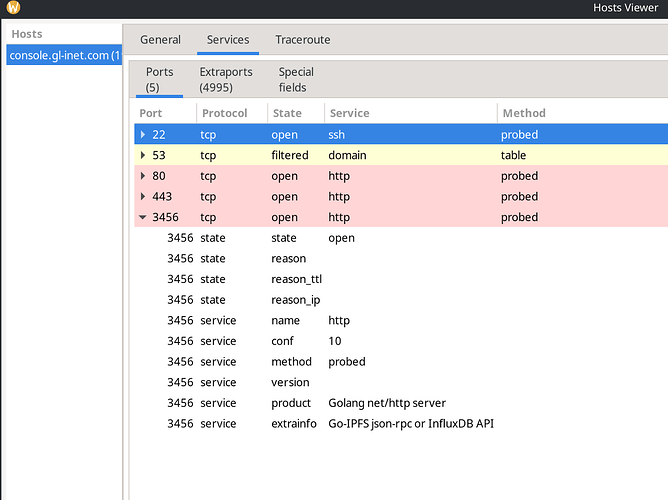
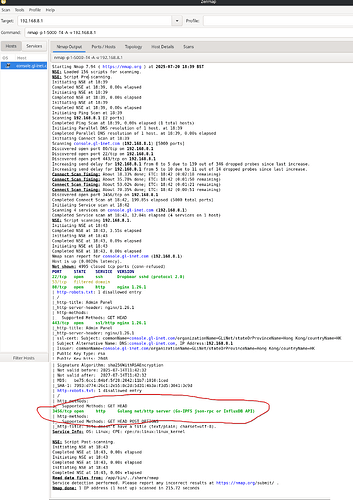
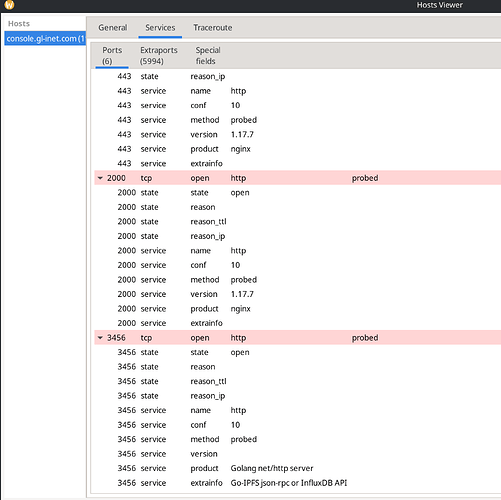
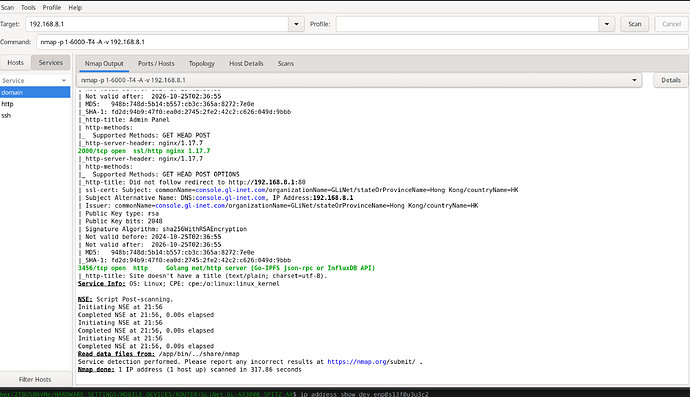
Anyway my router originally had two ports open, other than the regular 22, 53, 80, 443; these were 2000 and 3456.
I bought the router in March 2025 but the pepetrators got the leap on me at some point and it's been a nightmare as I'm not a computer wizard by any means. I thought updating via UBoot would be sufficient to remove any viruses but it seems not.
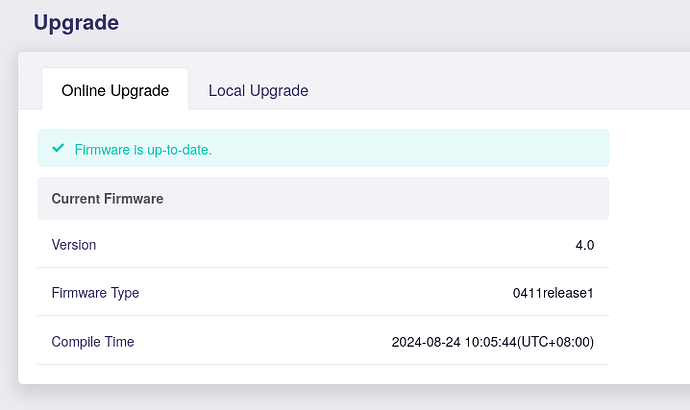
As soon as I could upgrade I did but I think I downloaded an infected .bin probably as they had poisoned my DNS. I downgraded from latest beta to v4.04 and then upgraded again to the latest beta. I managed to remove the open port 2000 but 3456 still remains open. I am on the latest UBoot, having just today updated, I then downgraded again to openwrt-x3000-4.0-0413r2.bin, still no change (i.e. port 3456 still open) and am now back on openwrt-x3000-4.8.0-0714-1752496086.bin.
How do I remove this?
I'm not ignoring the possibility this could be a supply chain attack but deleting all data and a number of firmware updates via UBoot have not got rid of this backdoor into my router.