Hi Everyone,
We’re headed to South America to help my husband’s family take care of his mother.
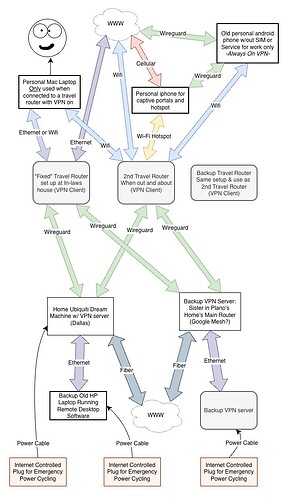
I’m a remote worker, and use my own laptop, but want to keep my location looking like Texas. I mostly use MS Office applications, Google web-applications, Zoom, and extremely rarely VPN into work from my Mac.
I have a Creta (GL-AR750), a Shadow (GL-AR300M16-Ext), and was given a XiaoMi 4A Gigabit router that has OpenWRT on it (I’ve tried to configure OpenWRT, but struggled).
I’d appreciate any advice on my setup and help with my hardware before we leave.
My sister in Plano has offered to let me plug a device into her router, but she doesn’t know much about router configuration.
We’ll mainly be at my mother-in-law’s, but we will also be staying in some hotels, and traveling a little, so I’d like to set up a “fixed” travel router as a VPN client and WIFI at my mother-in-law’s apartment, and have a small travel router for when we’re traveling. I was also thinking that it would be smart to have a backup travel router in case the small travel router breaks or is lost, etc.
I’m removing everything work-related from my iPhone, so I can’t see my work calendar or answer email on the go. So, to get around that, I was thinking of bringing an old android phone w/out a SIM card and an always-on wireguard client to use with hotspot or over non-captive wifi just for work email and calendar.
Questions:
- Any problems with this plan, or things we haven’t thought of?
- How can I most easily set up the VPN server behind my sister’s router? (somehow without port forwarding? Something else?)
- What hardware should I use for the various routers?
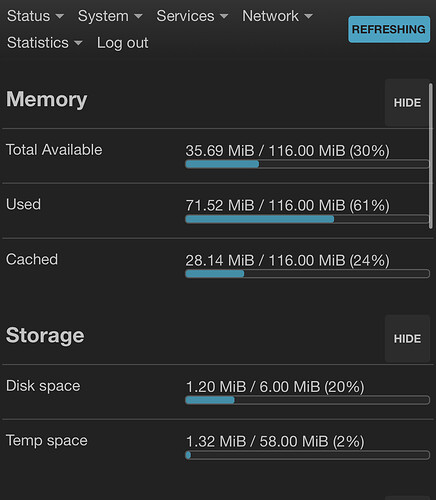
I was thinking maybe the XiaoMi with OpenWRT as the “Fixed” travel router at my mother-in-law’s for Wifi and VPN client, my Creta as my 2nd travel router when away from the apartment, the shadow with an external antenna as the backup travel router, and buying another shadow without an external antenna for the VPN server at my sister’s house. - I’m struggling with the OpenWRT, I haven’t been able to set it up as a travel VPN client. Any advice, or should I use it as a VPN server at my sister’s?
- Are the internet-controlled power switches overkill? I just wanted to be able to power cycle anything from a web-app like TP-Link’s Kasa.
I tried to make this diagram.
Any help would mean a lot,
Lane