Hey,
This is cross posed from someone 23 days ago on the ui.com forums but I chimed in yesterday as well. It was advised to also ask this question here. I’ve made some progress and can now ping the AXT1800 from my UDM network but now I need to figure out how to reach the 192.168.8.x subnet and the clients on it. Before I go in and break everything trying to figure this out myself I figured I’d just ask first lol.
Here is the post here: https://community.ui.com/questions/VPN-traffic-needs-firewall-rule-or-extra-routes/a12b24e9-d4a1-433a-9429-41121d8e0bb6
Here is a copy and paste of the simplest way to show what I’m trying to accomplish:
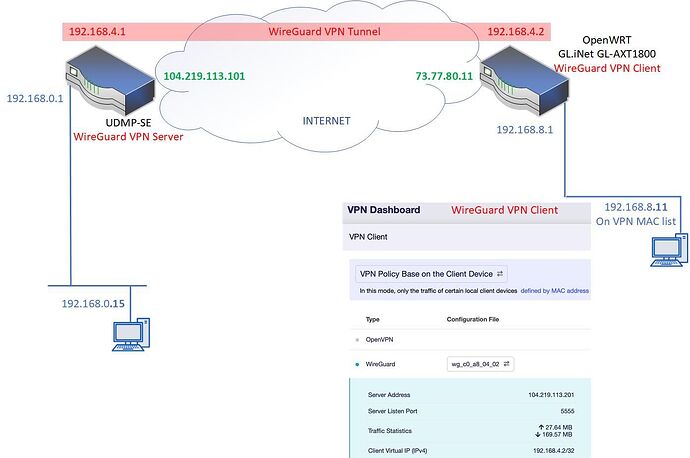
But here is a visual representation of my setup. I need to be able to ping from 192.168.8.11 to 1192.168.0.15 and the reverse ping from .15 to .11
And a copy/paste for my reasoning:
I just poked around a bit here for the last hour and I have to leave but 100% for sure you cannot set up static routes from the basic GUI. You need to go to the LUCI address and access the full OpenWRT section. From there I can set up routes correctly. I’ll dive into this further tomorrow but I tried drop in gateway mode and yeah, that didn’t work either. Stand by for more information tomorrow.
I will say this. My whole reason for doing this was to make it so that I can use non-inbound routable connections such as Verizon and T-Mobile 4G LTE/5G at remote radio tower sites that I have Cradlepoints at. If you think about it, if you cannot configure inbound routing (The cell towers assign regular class B NAT’ed IP’s) then this device will not work for MY SPECIFIC usage case. For yours, if you have inbound routing enabled by your ISP then it should work but you’d have to put routes in on the LUCI GUI.
I’ll mess with this more for sure but I’m 99.99% sure this won’t work for my usage case with Dynamic IP Verizon 4G/5G connections sitting on Cradlepoints.
Nailed it!!
In both of my circumstances I don’t have the ability to open a firewall for any inbound IP IPSec site to site traffic to flow to. That’s why I am trying to get this to work with the client. On the ride to the gym I was visualizing in my head that it should work because literally if you’re putting a route in the next hop would be the wire guard VPN which has basically a static IP address when connected that is always asigned from the ubiquiti udm Pro out to that device. I’m going to play with it tomorrow when my brain isn’t absolutely fried from working 10 hours on other firewall things for other clients.
As far as being able to Ping what would be the Wan interface on the wire guard client side router (the ATX1800), you would not normally have that ability because it would be blocked from the security rules. I’m going to have to open that up in the test environment to prove it so that way I can at least attempt to Ping that router from a device on the main ubiquiti Network. Once I could get a good ping on that router then I would focus on getting routes put in to Route the traffic to the devices on the other side of the router (LAN side).
I may go post on the other manufacturers web form tomorrow as well. Or probably later tonight to see if anyone else has done this because this is fairly new stuff for me and I’m obviously pushing the limits for what you should and shouldn’t be able to do lol. Either way if there’s a will there’s got to be a way for me to get it done LOL
Today I did find the “Allow Remote Access LAN” button and now can ping the wan interface of the Wireguard (192.168.201.4)
Thanks for anyones help on this! ![]()