Hi there ![]()
Many GL.iNet users have asked how to set up Let's Encrypt so that the router receives a valid SSL certificate and can be accessed via their xxxxxx.glddns.com address without receiving a certificate warning.
I've created a script that automates this entire process - including automatic renewal ![]()
Key Features
 Automatic SSL/TLS Certificates - Requests and installs Let's Encrypt certificates
Automatic SSL/TLS Certificates - Requests and installs Let's Encrypt certificates Auto-Renewal - Certificates renew automatically via cron job (daily at 00:00)
Auto-Renewal - Certificates renew automatically via cron job (daily at 00:00) DDNS Integration - Works seamlessly with GL.iNet DDNS
DDNS Integration - Works seamlessly with GL.iNet DDNS Nginx Configuration - Automatically configures nginx for HTTPS
Nginx Configuration - Automatically configures nginx for HTTPS Validation Checks - Verifies DDNS and public IP match before proceeding
Validation Checks - Verifies DDNS and public IP match before proceeding Persistence - Optional: Make installation persistent across firmware upgrades
Persistence - Optional: Make installation persistent across firmware upgrades Restore Function - Easy restoration to factory default configuration
Restore Function - Easy restoration to factory default configuration
Permanent Installation
During installation, you'll be asked if you want to make it permanent across firmware updates. If you choose "yes", the certificate files and nginx configuration will be preserved during firmware upgrades by adding them to /etc/sysupgrade.conf.
Prerequisites
To execute the script, the following requirements must be met:
- A GL.iNet router with the latest GL firmware version
- A working internet connection
- DDNS must be enabled and configured!
- DDNS IP must be the same as the router's public IP (will be checked by the script)
- Using a router behind CGNAT is not supported
![]() Important: The script will request a certificate for the router's public IP. VPN IP is not supported.
Important: The script will request a certificate for the router's public IP. VPN IP is not supported.
Quick-Start
You can run it directly on your router via SSH with this single command:
wget https://get.admon.me/acme-update -O enable-acme.sh && sh enable-acme.sh
Follow the on-screen instructions to complete the ACME setup.
Download & Documentation
Advanced Usage
Running without confirmation
Use the --force flag to run the script without any confirmation prompts for fully unattended installations.
sh enable-acme.sh --force
Manual Certificate Renewal
While certificates renew automatically, you can manually trigger renewal:
sh enable-acme.sh --renew
Or if you installed the script to /usr/bin:
/usr/bin/enable-acme --renew
Logging options
Enable timestamps for debugging:
sh enable-acme.sh --log
Use ASCII characters instead of emojis for older terminals:
sh enable-acme.sh --ascii
Usage
./enable-acme.sh [--renew] [--restore] [--force] [--log] [--ascii] [--help]
| Argument | Description |
|---|---|
--renew |
Manually renew the ACME certificate |
--restore |
Restore nginx to factory default configuration |
--force |
Skip all confirmation prompts (for unattended installation) |
--log |
Show timestamps in log messages |
--ascii |
Use ASCII characters instead of emojis for compatibility |
--help |
Display help message with all available arguments |
Automatic Renewal
The certificate will be renewed automatically by a cronjob installed by the script. The cronjob checks for renewal every day at 00:00.
No manual intervention is required – just let it run!
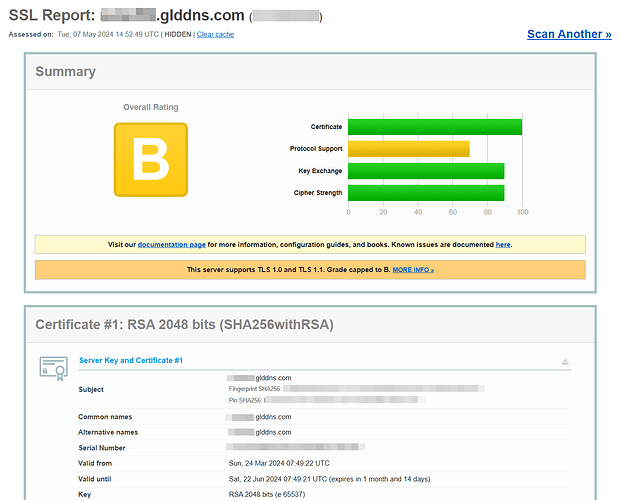
Result
Disclaimer
This script is provided as-is without any warranty. Use it at your own risk.
It may potentially:
 Break your router, computer, or network
Break your router, computer, or network Cause unexpected system behavior
Cause unexpected system behavior Even burn down your house (okay, probably not, but you get the idea)
Even burn down your house (okay, probably not, but you get the idea)
You have been warned!
Restoring
Simply run the script with the --restore argument:
sh enable-acme.sh --restore
This will restore HTTP access on port 80, revert to self-signed certificates, remove ACME configuration and restart nginx.
Manual Restoration:
You can also manually revert the changes with these commands:
sed -i 's/#listen 80;/listen 80;/g' /etc/nginx/conf.d/gl.conf
sed -i 's/#listen \[::\]:80;/listen \[::\]:80;/g' /etc/nginx/conf.d/gl.conf
sed -i 's|ssl_certificate .*;|ssl_certificate /etc/nginx/nginx.cer;|g' /etc/nginx/conf.d/gl.conf
sed -i 's|ssl_certificate_key .*;|ssl_certificate_key /etc/nginx/nginx.key;|g' /etc/nginx/conf.d/gl.conf
/etc/init.d/nginx restart
Made with ![]() by @Admon
by @Admon
If you find this helpful, consider supporting the project via GitHub