Hello,
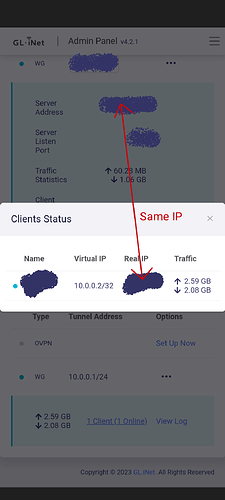
I’m using a GL-AX1800 Flint on 4.2.1 beta4 firmware, where I’m using VPN cascading. I have then 2 VPN connections chaining, one between end-device (like a smartphone) → GL-iNet router (let’s call it VPN1), and one between GL-iNet router → VPN service provider (let’s call it VPN2). When I’m away from home, this works pretty fine, my phone goes through VPN1 then VPN2. However, when I’m at home (and then already directly connected to the router), it seems using VPN2 to reach the VPN1 connection address, because the router doesn’t seem to realize it is itself the destination of the connection, and then it makes VPN2 → VPN1 → VPN2. I noticed this because I saw that the IP of the client connected to the WG server was the same than the server address of the VPN client.
Of course, going through VPN2 twice isn’t much useful. One solution I’ve found to optimize this, is to enable Dynamic DNS, use the glddns address as VPN1 destination, and I edited the hosts file in the router to manually define xxxxxx.glddns.com address to resolve as 192.168.8.1. Then, when I’m at home, VPN1 client IP is now a 192.168.8.X address. But I have to restart the WG connection on my phone everytime I get away from home and 192.168.8.1 isn’t reachable anymore, to force a new resolution of xxxxx.glddns.com.
Is there a better solution for this situation ?