Wed Nov 19 21:46:15 2025 daemon.notice netifd: Network device 'wgclient' link is down
Wed Nov 19 21:46:15 2025 user.notice firewall: Reloading firewall due to ifdown of wgclient ()
Wed Nov 19 21:46:15 2025 daemon.notice netifd: Interface 'wgclient' is now down
Wed Nov 19 21:46:15 2025 daemon.notice netifd: Interface 'wgclient' is setting up now
Wed Nov 19 21:46:36 2025 daemon.notice netifd: Network device 'wgclient' link is up
Wed Nov 19 21:46:36 2025 daemon.notice netifd: Interface 'wgclient' is now up
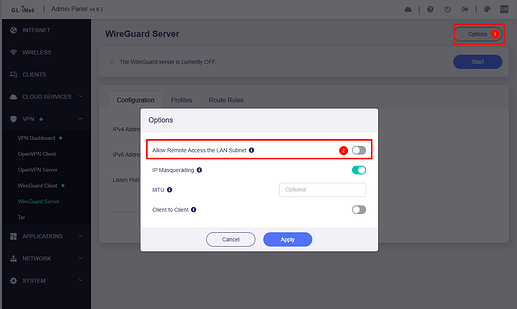
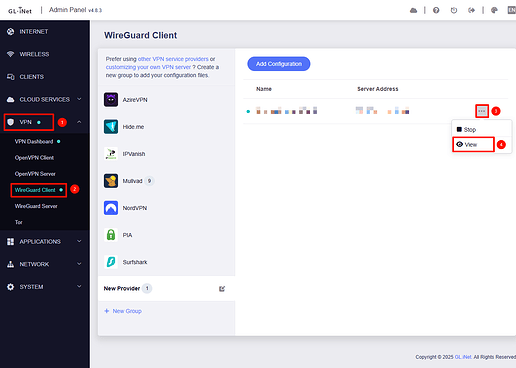
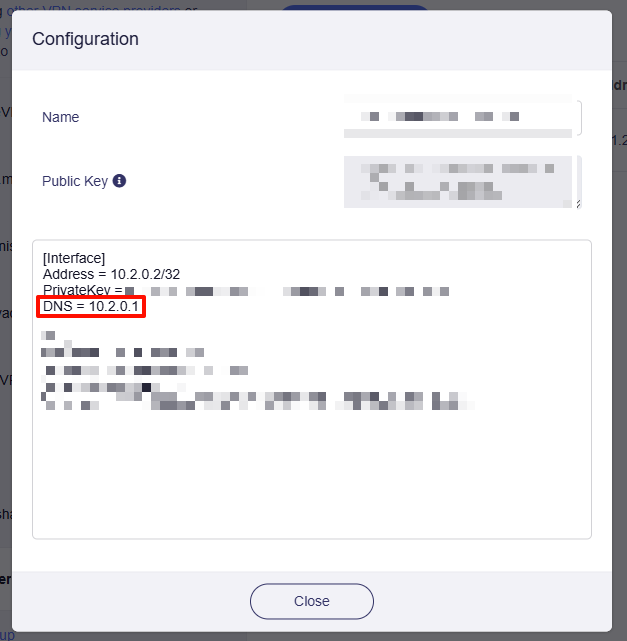
I have been running into this problem quite often the last few days. I am using a double GLINet Slate AXT1800 setup (one client and one server) and a Wireguard VPN. My internet intermittently cuts out and I see the above in the logs. It lasts for between a few seconds and several minutes before service is restored.
The disruption doesn’t appear to be regarding to my local internet connection as that always is working fine even when my VPN is down. Nor am I experiencing any power issues in my local site that might cause such an issue.
I understand it is difficult to debug issues like this from afar - but just wondering what, if any, steps I should take to try to understand what the problem is here? Thanks in advance for the help.
Edit #1: I have been using this setup for about two months without any issues, in the last few days is the first time I've had this issue. As far as I know, neither the config and properties of the networks have changed
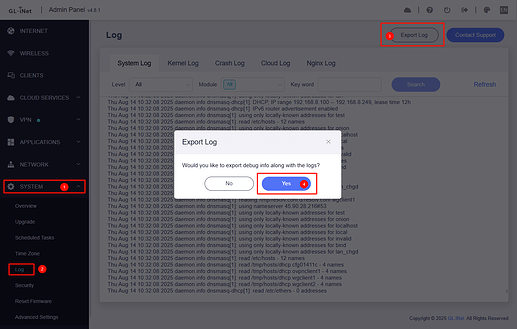
Edit #2: I also captured the following more extended output from the logread output:
Wed Nov 19 21:46:15 2025 daemon.info dnsmasq[6676]: exiting on receipt of SIGTERMWed Nov 19 21:46:15 2025 daemon.notice netifd: Network device 'wgclient' link is downWed Nov 19 21:46:15 2025 user.notice firewall: Reloading firewall due to ifdown of wgclient ()Wed Nov 19 21:46:15 2025 daemon.notice netifd: Interface 'wgclient' is now downWed Nov 19 21:46:15 2025 daemon.notice netifd: Interface 'wgclient' is setting up nowWed Nov 19 21:46:15 2025 daemon.err dnsmasq[4163]: failed to send packet: Operation not permittedWed Nov 19 21:46:36 2025 daemon.notice netifd: Network device 'wgclient' link is upWed Nov 19 21:46:36 2025 daemon.notice netifd: Interface 'wgclient' is now upWed Nov 19 21:46:36 2025 user.notice wgclient-up: env value:T_J_V_ifname=string J_V_address_external=1 USER=root ifname=wgclient ACTION=KEYPAIR-CREATED N_J_V_address_external=address-external SHLVL=3 J_V_keep=1 HOME=/ HOTPLUG_TYPE=wireguard T_J_V_interface=string J_V_ifname=wgclient T_J_V_link_up=boolean LOGNAME=root DEVICENAME= T_J_V_action=int TERM=linux SUBSYSTEM=wireguard PATH=/usr/sbin:/usr/bin:/sbin:/bin CONFIG_LIST_STATE= J_V_interface=wgclient K_J_V= action ifname link_up address_external keep interface J_V_link_up=1 J_V_action=0 T_J_V_address_external=boolean N_J_V_link_up=link-up T_J_V_keep=boolean PWD=/ JSON_CUR=J_V CONFIG_SECTIONS=global AzireVPN Mullvad FromApp group_3404 group_2722 group_5689 group_941 peer_4525 CONFIG_cfg030f15_ports=Wed Nov 19 21:46:36 2025 user.notice firewall: Reloading firewall due to ifup of wgclient (wgclient)Wed Nov 19 21:46:37 2025 daemon.info dnsmasq[9560]: Connected to system UBusWed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: started, version 2.85 cache disabledWed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: DNS service limited to local subnetsWed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: compile time options: IPv6 GNU-getopt no-DBus UBus no-i18n no-IDN DHCP DHCPv6 no-Lua TFTP conntrack ipset auth cryptohash DNSSEC no-ID loop-detect inotify dumpfileWed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: UBus support enabled: connected to system busWed Nov 19 21:46:37 2025 daemon.info dnsmasq-dhcp[9562]: DHCP, IP range 192.168.8.100 -- 192.168.8.249, lease time 12hWed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: using only locally-known addresses for domain testWed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: using only locally-known addresses for domain onionWed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: using only locally-known addresses for domain localhostWed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: using only locally-known addresses for domain localWed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: using only locally-known addresses for domain invalidWed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: using only locally-known addresses for domain bindWed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: using only locally-known addresses for domain lanWed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: using nameserver 64.6.64.6#53Wed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: read /etc/hosts - 4 addressesWed Nov 19 21:46:37 2025 daemon.info dnsmasq[9562]: read /tmp/hosts/dhcp.cfg01411c - 3 addressesWed Nov 19 21:46:37 2025 daemon.info dnsmasq-dhcp[9562]: read /etc/ethers - 0 addresses