Maybe one of the armchair experts here should start their own router company, which would no doubt never release any imperfect software ![]()
Check logs, I had to untick "use provided" DNS on WAN interface and insert 8.8.8.8 to get ddns running.
Sometimes with version upgrades I need to reinstall packages - have you tried that?
@GL.iNet Staff version 4.8.0-op24 Beta 2025-07-29 runs without problems so far, thank you !
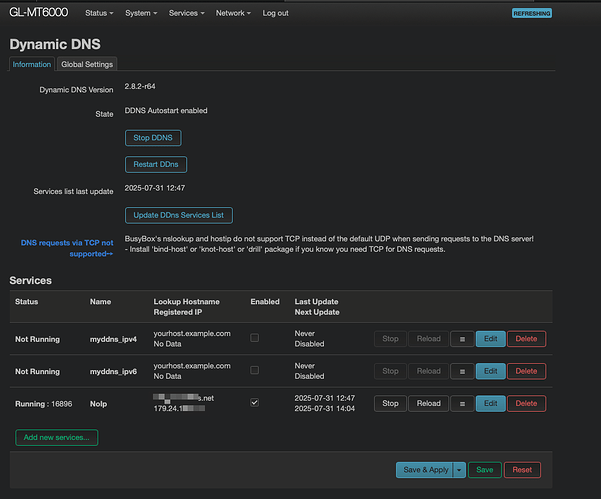
Hello, using Beta 4.8.0 op24 on Flint 2 here, WireGuard in client mode works without problems; the problem is that No-Ip.com DDNS does not work, whereas in the stable version 4.7.7 it worked without problems.
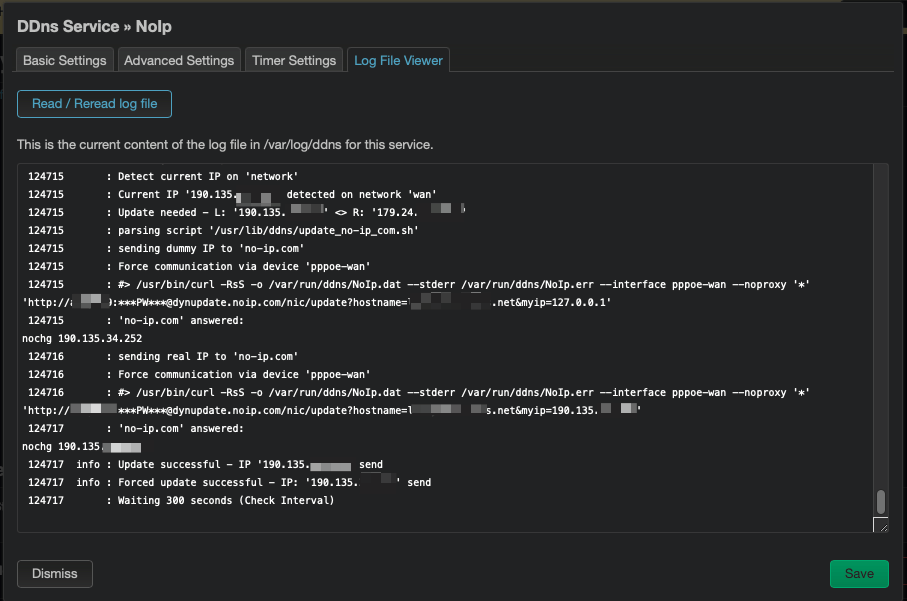
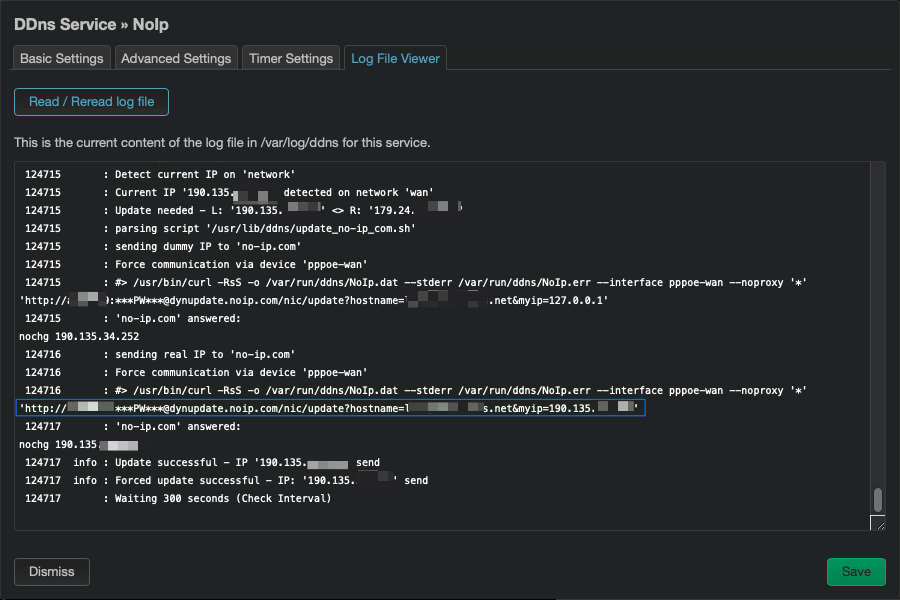
Log:
openwrt-mt3000-4.8.0-op24-0729-1753791349.bin
gl-repeater does not auto select the correct/none encryption.
saved repeater setting from previous firmware version is fine but new repeater input does not.
log
daemon.info gl-repeater[xxxx]: (repeater.lua:xxx) connecting to bss: SSID MAC <ch> none
/etc/config/repeater
config network
option ssid 'SSID'
option key 'PASSWORD'
option proto 'dhcp'
option network 'wwan'
option auto_portal '0'
option disguise '0'
option selected '1'
/etc/config/wireless
config wifi-iface 'sta'
option mode 'sta'
option ifname 'sta1'
option device 'radio1'
option network 'wwan'
option ssid 'SSID'
option bssid 'MAC'
option macaddr 'MAC2'
option key 'PASSWORD'
option encryption 'none'
Does the NoIP DDNS still resolve even though the endpoint didn't accept the device side's script push attempt? I've seen other DDNS providers not accept the push as there's been no IP change require updating. drill $myNoIPDDNSHere
opkg update && opkg install drill
The strange thing is that with firmware 4.7.7 it works perfectly. From what I could see in this 4.8 version, No-Ip.com responds with bad authentication. Even though the IP is the same, the script forces NoIp to accept it. If I copy the URL provided in the log and paste it into the browser, the IP update is performed.
How strange. What version is ddns-scripts-noip showing as?
opkg list-installed | grep 'ddns-scripts-noip'
Here, in case you need to downgrade to compare the last 'known good' but want to keep the current state's confs:
opkg update && opkg install openssh-sftp-server
The current version of ddns-scripts-noip that doesn't work is 2.8.2-r64, the last one that works is 2.8.2-12
It sounds like you've identified a problem with the upstream sources. Do you have a diff tool to compare the scripts? If not Beyond Compare is quite good & has a 30 day trial.
Thanks. I have a Beyond Compare 5 license and there are differences in the files dynamic_dns_functions.sh, dynamic_dns_lucihelper.sh, and dynamic_dns_updater.sh, mainly in the functions for obtaining the IP. Firmware 4.7.7 talks about obtaining the local IP, while firmware 4.8.0 talks about obtaining the current IP.
Well, assuming those are baked into the scripts & not configurable options you seem to have discovered a bug between the two ddns-scripts-noip packages.
I don't use No-IP but is 2.8.2-r64 set to use ip_source='web' & use_https='1' on interface='wan' on a ip_url?
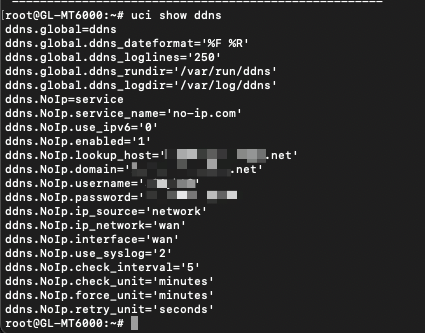
uci show ddns
I'm running ddns-scripts & ddns-scripts-services v2.8.2-12. My IP updates use ip_source='web' with https, cacert & ip_url. I don't see those lines in your output. You may have to edit/add them to your ddns conf.
Here's something to compare against but again I don't use No-IP so there may be No-IP specific requirements:
cat /etc/config/ddns
config service 'my_ddns_srv'
option interface 'wan'
option service_name 'my-ddns-provider-here'
option lookup_host 'my_ddns_domain_here'
option domain 'my_ddns_domain_here'
option username 'username'
option password 'password'
option ip_source 'web'
option use_https '1'
option cacert '/etc/ssl/certs'
option ip_url 'https://ipcheck.my-ddns-provider-here.com/'
option enabled '1'
In place upgrading from version 4.7.5 OP to the latest build of 4.8 OP, I successfully saved my settings without encountering any issues. The only modules currently running are:
- General Routing: No acceleration with 15 IP reservations
- WireGuard Server: With three client configurations
- Adguard Home
- WDS Parent: With three Marble child routers running the latest 4.7 beta
Despite encountering a panic/crash, I was unable to pinpoint the exact time of occurrence. Overall, I have a positive impression that this release is more stable than the one I upgraded from. Here are the logs:
Oops#1 Part1
<6>[130101.160166] mt798x-wmac 18000000.wifi wlan1.sta2 (unregistering): left promiscuous mode
<6>[130101.168263] br-lan: port 8(wlan1.sta2) entered disabled state
<6>[130245.434120] br-lan: port 8(wlan1.sta2) entered blocking state
<6>[130245.439992] br-lan: port 8(wlan1.sta2) entered disabled state
<6>[130245.445869] mt798x-wmac 18000000.wifi wlan1.sta2: entered allmulticast mode
<6>[130245.453195] mt798x-wmac 18000000.wifi wlan1.sta2: entered promiscuous mode
<6>[130245.460324] br-lan: port 8(wlan1.sta2) entered blocking state
<6>[130245.466146] br-lan: port 8(wlan1.sta2) entered forwarding state
<6>[130245.472665] mt798x-wmac 18000000.wifi wlan1.sta2: left allmulticast mode
<6>[130245.479588] mt798x-wmac 18000000.wifi wlan1.sta2: left promiscuous mode
<6>[130245.486499] br-lan: port 8(wlan1.sta2) entered disabled state
<6>[130245.557402] br-lan: port 8(wlan1.sta2) entered blocking state
<6>[130245.563278] br-lan: port 8(wlan1.sta2) entered disabled state
<6>[130245.569329] mt798x-wmac 18000000.wifi wlan1.sta2: entered allmulticast mode
<6>[130245.576643] mt798x-wmac 18000000.wifi wlan1.sta2: entered promiscuous mode
<6>[130245.583744] br-lan: port 8(wlan1.sta2) entered blocking state
<6>[130245.589585] br-lan: port 8(wlan1.sta2) entered forwarding state
<1>[150863.218855] Unable to handle kernel paging request at virtual address 001e328a8304a7a7
<1>[150863.226895] Mem abort info:
<1>[150863.229778] ESR = 0x0000000096000004
<1>[150863.233626] EC = 0x25: DABT (current EL), IL = 32 bits
<1>[150863.239017] SET = 0, FnV = 0
<1>[150863.242144] EA = 0, S1PTW = 0
<1>[150863.245371] FSC = 0x04: level 0 translation fault
<1>[150863.250319] Data abort info:
<1>[150863.253278] ISV = 0, ISS = 0x00000004, ISS2 = 0x00000000
<1>[150863.258832] CM = 0, WnR = 0, TnD = 0, TagAccess = 0
<1>[150863.263960] GCS = 0, Overlay = 0, DirtyBit = 0, Xs = 0
<1>[150863.269343] [001e328a8304a7a7] address between user and kernel address ranges
<0>[150863.276550] Internal error: Oops: 0000000096000004 [#1] SMP
<7>[150863.282191] Modules linked in: pppoe ppp_async option wireguard usb_wwan rndis_host qmi_wwan pppox ppp_generic nft_fib_inet nf_flow_table_inet mt7915e(O) mt76_connac_lib(O) mt76(O) mac80211(O) libchacha20poly1305 ipt_REJECT huawei_cdc_ncm chacha_neon cfg80211(O) cdc_ncm cdc_ether xt_time xt_tcpudp xt_tcpmss xt_statistic xt_state xt_recent xt_quota xt_pkttype xt_owner xt_nat xt_multiport xt_mark xt_mac xt_limit xt_length xt_hl xt_helper xt_ecn xt_dscp xt_conntrack xt_connmark xt_connlimit xt_connbytes xt_comment xt_cgroup xt_addrtype xt_TPROXY xt_TCPMSS xt_REDIRECT xt_MASQUERADE xt_LOG xt_HL xt_DSCP xt_CT xt_CLASSIFY usbserial usbnet ts_fsm ts_bm slhc poly1305_neon nft_tproxy nft_socket nft_reject_ipv6 nft_reject_ipv4 nft_reject_inet nft_reject nft_redir nft_quota nft_numgen nft_nat nft_masq nft_log nft_limit nft_hash nft_flow_offload nft_fib_ipv6 nft_fib_ipv4 nft_fib nft_ct nft_compat nft_chain_nat nf_tproxy_ipv6 nf_tproxy_ipv4 nf_tables nf_socket_ipv6 nf_socket_ipv4 nf_reject_ipv4 nf_nat_tftp nf_nat_snmp_basic
<7>[150863.282371] nf_nat_pptp nf_nat_irc nf_nat_h323 nf_nat_amanda nf_log_syslog nf_flow_table nf_conntrack_tftp nf_conntrack_snmp nf_conntrack_sane nf_conntrack_pptp nf_conntrack_netlink nf_conntrack_netbios_ns nf_conntrack_irc nf_conntrack_h323 nf_conntrack_broadcast ts_kmp nf_conntrack_amanda nf_conncount mdio_netlink(O) libcurve25519_generic libcrc32c libchacha iptable_nat iptable_mangle iptable_filter ipt_ECN ipheth ip6table_raw ip_tables compat(O) cdc_wdm cdc_acm br_netfilter asn1_decoder arptable_filter arpt_mangle arp_tables fuse sch_tbf sch_ingress sch_htb sch_hfsc em_u32 cls_u32 cls_route cls_matchall cls_fw cls_flow cls_basic act_skbedit act_mirred act_gact xt_set ip_set_list_set ip_set_hash_netportnet ip_set_hash_netport ip_set_hash_netnet ip_set_hash_netiface ip_set_hash_net ip_set_hash_mac ip_set_hash_ipportnet ip_set_hash_ipportip ip_set_hash_ipport ip_set_hash_ipmark ip_set_hash_ipmac ip_set_hash_ip ip_set_bitmap_port ip_set_bitmap_ipmac ip_set_bitmap_ip ip_set nfnetlink ip6table_nat nf_nat nf_conntrack
<7>[150863.371949] nf_defrag_ipv6 nf_defrag_ipv4 ip6t_NPT ip6table_mangle ip6table_filter ip6_tables ip6t_REJECT x_tables nf_reject_ipv6 ifb udp_diag tcp_diag raw_diag inet_diag veth tun ovpn_dco_v2(O) udp_tunnel ip6_udp_tunnel dns_mark(O) ntfs nls_utf8 nls_iso8859_1 nls_cp437 seqiv geniv chacha20poly1305 uas usb_storage leds_gpio xhci_plat_hcd xhci_pci xhci_mtk_hcd xhci_hcd uhci_hcd ohci_platform ohci_hcd fsl_mph_dr_of ehci_platform ehci_fsl kmwan(O) ehci_hcd gpio_button_hotplug(O) gl_sdk4_tertf(O) gl_repeater(O) gl_sdk4_black_white_list(O) vfat fat exfat usbcore usb_common aquantia mii gl_sdk4_hw_info(O)
<7>[150863.514880] CPU: 3 PID: 30866 Comm: gl_led Tainted: G O 6.6.93 #0
<7>[150863.522431] Hardware name: GL.iNet GL-MT6000 (DT)
<7>[150863.527204] pstate: 20400005 (nzCv daif +PAN -UAO -TCO -DIT -SSBS BTYPE=--)
<7>[150863.534232] pc : kmem_cache_alloc_node+0xbc/0x2d0
<7>[150863.539014] lr : kmem_cache_alloc_node+0x48/0x2d0
<7>[150863.543787] sp : ffffffc08a07b9a0
<7>[150863.547171] x29: ffffffc08a07b9a0 x28: 0000000000000000 x27: ffffffc08109fda8
<7>[150863.554373] x26: 0000000000000cc0 x25: 0000000000000048 x24: 00000000ffffffff
<7>[150863.561576] x23: ffffffc08024a8c8 x22: 0000000000000cc0 x21: 0000000000000000
<7>[150863.568779] x20: ffffffc080eae000 x19: ffffff8000004600 x18: 0000000000000000
<7>[150863.575981] x17: 0000000000000000 x16: 0000000000000000 x15: 0000000000000000
<7>[150863.583183] x14: 0000000000000000 x13: 0000000000000000 x12: 0000000000000000
<7>[150863.590385] x11: 0000000000000000 x10: 0000000000000000 x9 : ffffffc080266f48
<7>[150863.597588] x8 : ffffff801d5e6b80 x7 : 0000000000000000 x6 : 0000000000000000
<7>[150863.604791] x5 : d6c683a803fb5878 x4 : 0000000000038757 x3 : a7a704838a321e0f
<7>[150863.611993] x2 : 0000000000038756 x1 : 0000000000000020 x0 : 0f1e328a8304a787
<7>[150863.619196] Call trace:
<7>[150863.621715] kmem_cache_alloc_node+0xbc/0x2d0
<7>[150863.626143] alloc_vmap_area+0xc8/0x8f8
<7>[150863.630053] __get_vm_area_node+0xbc/0x1b0
<7>[150863.634221] __vmalloc_node_range+0x114/0x710
<7>[150863.638647] copy_process+0x9cc/0x1408
<7>[150863.642469] kernel_clone+0x80/0x488
<7>[150863.646116] __do_sys_clone+0x5c/0x78
<7>[150863.649849] __arm64_sys_clone+0x24/0x38
<7>[150863.653843] invoke_syscall.constprop.0+0x54/0xf0
<7>[150863.658618] do_el0_svc+0x44/0xc8
<7>[150863.662006] el0_svc+0x18/0x50
<7>[150863.665134] el0t_64_sync_handler+0x118/0x128
<7>[150863.669561] el0t_64_sync+0x150/0x158
<0>[150863.673297] Code: b9402a61 f9405e65 8b010003 dac00c63 (f8616801)
<4>[150863.679457] ---[ end trace 0000000000000000 ]---
Panic#2 Part1
<6>[130245.445869] mt798x-wmac 18000000.wifi wlan1.sta2: entered allmulticast mode
<6>[130245.453195] mt798x-wmac 18000000.wifi wlan1.sta2: entered promiscuous mode
<6>[130245.460324] br-lan: port 8(wlan1.sta2) entered blocking state
<6>[130245.466146] br-lan: port 8(wlan1.sta2) entered forwarding state
<6>[130245.472665] mt798x-wmac 18000000.wifi wlan1.sta2: left allmulticast mode
<6>[130245.479588] mt798x-wmac 18000000.wifi wlan1.sta2: left promiscuous mode
<6>[130245.486499] br-lan: port 8(wlan1.sta2) entered disabled state
<6>[130245.557402] br-lan: port 8(wlan1.sta2) entered blocking state
<6>[130245.563278] br-lan: port 8(wlan1.sta2) entered disabled state
<6>[130245.569329] mt798x-wmac 18000000.wifi wlan1.sta2: entered allmulticast mode
<6>[130245.576643] mt798x-wmac 18000000.wifi wlan1.sta2: entered promiscuous mode
<6>[130245.583744] br-lan: port 8(wlan1.sta2) entered blocking state
<6>[130245.589585] br-lan: port 8(wlan1.sta2) entered forwarding state
<1>[150863.218855] Unable to handle kernel paging request at virtual address 001e328a8304a7a7
<1>[150863.226895] Mem abort info:
<1>[150863.229778] ESR = 0x0000000096000004
<1>[150863.233626] EC = 0x25: DABT (current EL), IL = 32 bits
<1>[150863.239017] SET = 0, FnV = 0
<1>[150863.242144] EA = 0, S1PTW = 0
<1>[150863.245371] FSC = 0x04: level 0 translation fault
<1>[150863.250319] Data abort info:
<1>[150863.253278] ISV = 0, ISS = 0x00000004, ISS2 = 0x00000000
<1>[150863.258832] CM = 0, WnR = 0, TnD = 0, TagAccess = 0
<1>[150863.263960] GCS = 0, Overlay = 0, DirtyBit = 0, Xs = 0
<1>[150863.269343] [001e328a8304a7a7] address between user and kernel address ranges
<0>[150863.276550] Internal error: Oops: 0000000096000004 [#1] SMP
<7>[150863.282191] Modules linked in: pppoe ppp_async option wireguard usb_wwan rndis_host qmi_wwan pppox ppp_generic nft_fib_inet nf_flow_table_inet mt7915e(O) mt76_connac_lib(O) mt76(O) mac80211(O) libchacha20poly1305 ipt_REJECT huawei_cdc_ncm chacha_neon cfg80211(O) cdc_ncm cdc_ether xt_time xt_tcpudp xt_tcpmss xt_statistic xt_state xt_recent xt_quota xt_pkttype xt_owner xt_nat xt_multiport xt_mark xt_mac xt_limit xt_length xt_hl xt_helper xt_ecn xt_dscp xt_conntrack xt_connmark xt_connlimit xt_connbytes xt_comment xt_cgroup xt_addrtype xt_TPROXY xt_TCPMSS xt_REDIRECT xt_MASQUERADE xt_LOG xt_HL xt_DSCP xt_CT xt_CLASSIFY usbserial usbnet ts_fsm ts_bm slhc poly1305_neon nft_tproxy nft_socket nft_reject_ipv6 nft_reject_ipv4 nft_reject_inet nft_reject nft_redir nft_quota nft_numgen nft_nat nft_masq nft_log nft_limit nft_hash nft_flow_offload nft_fib_ipv6 nft_fib_ipv4 nft_fib nft_ct nft_compat nft_chain_nat nf_tproxy_ipv6 nf_tproxy_ipv4 nf_tables nf_socket_ipv6 nf_socket_ipv4 nf_reject_ipv4 nf_nat_tftp nf_nat_snmp_basic
<7>[150863.282371] nf_nat_pptp nf_nat_irc nf_nat_h323 nf_nat_amanda nf_log_syslog nf_flow_table nf_conntrack_tftp nf_conntrack_snmp nf_conntrack_sane nf_conntrack_pptp nf_conntrack_netlink nf_conntrack_netbios_ns nf_conntrack_irc nf_conntrack_h323 nf_conntrack_broadcast ts_kmp nf_conntrack_amanda nf_conncount mdio_netlink(O) libcurve25519_generic libcrc32c libchacha iptable_nat iptable_mangle iptable_filter ipt_ECN ipheth ip6table_raw ip_tables compat(O) cdc_wdm cdc_acm br_netfilter asn1_decoder arptable_filter arpt_mangle arp_tables fuse sch_tbf sch_ingress sch_htb sch_hfsc em_u32 cls_u32 cls_route cls_matchall cls_fw cls_flow cls_basic act_skbedit act_mirred act_gact xt_set ip_set_list_set ip_set_hash_netportnet ip_set_hash_netport ip_set_hash_netnet ip_set_hash_netiface ip_set_hash_net ip_set_hash_mac ip_set_hash_ipportnet ip_set_hash_ipportip ip_set_hash_ipport ip_set_hash_ipmark ip_set_hash_ipmac ip_set_hash_ip ip_set_bitmap_port ip_set_bitmap_ipmac ip_set_bitmap_ip ip_set nfnetlink ip6table_nat nf_nat nf_conntrack
<7>[150863.371949] nf_defrag_ipv6 nf_defrag_ipv4 ip6t_NPT ip6table_mangle ip6table_filter ip6_tables ip6t_REJECT x_tables nf_reject_ipv6 ifb udp_diag tcp_diag raw_diag inet_diag veth tun ovpn_dco_v2(O) udp_tunnel ip6_udp_tunnel dns_mark(O) ntfs nls_utf8 nls_iso8859_1 nls_cp437 seqiv geniv chacha20poly1305 uas usb_storage leds_gpio xhci_plat_hcd xhci_pci xhci_mtk_hcd xhci_hcd uhci_hcd ohci_platform ohci_hcd fsl_mph_dr_of ehci_platform ehci_fsl kmwan(O) ehci_hcd gpio_button_hotplug(O) gl_sdk4_tertf(O) gl_repeater(O) gl_sdk4_black_white_list(O) vfat fat exfat usbcore usb_common aquantia mii gl_sdk4_hw_info(O)
<7>[150863.514880] CPU: 3 PID: 30866 Comm: gl_led Tainted: G O 6.6.93 #0
<7>[150863.522431] Hardware name: GL.iNet GL-MT6000 (DT)
<7>[150863.527204] pstate: 20400005 (nzCv daif +PAN -UAO -TCO -DIT -SSBS BTYPE=--)
<7>[150863.534232] pc : kmem_cache_alloc_node+0xbc/0x2d0
<7>[150863.539014] lr : kmem_cache_alloc_node+0x48/0x2d0
<7>[150863.543787] sp : ffffffc08a07b9a0
<7>[150863.547171] x29: ffffffc08a07b9a0 x28: 0000000000000000 x27: ffffffc08109fda8
<7>[150863.554373] x26: 0000000000000cc0 x25: 0000000000000048 x24: 00000000ffffffff
<7>[150863.561576] x23: ffffffc08024a8c8 x22: 0000000000000cc0 x21: 0000000000000000
<7>[150863.568779] x20: ffffffc080eae000 x19: ffffff8000004600 x18: 0000000000000000
<7>[150863.575981] x17: 0000000000000000 x16: 0000000000000000 x15: 0000000000000000
<7>[150863.583183] x14: 0000000000000000 x13: 0000000000000000 x12: 0000000000000000
<7>[150863.590385] x11: 0000000000000000 x10: 0000000000000000 x9 : ffffffc080266f48
<7>[150863.597588] x8 : ffffff801d5e6b80 x7 : 0000000000000000 x6 : 0000000000000000
<7>[150863.604791] x5 : d6c683a803fb5878 x4 : 0000000000038757 x3 : a7a704838a321e0f
<7>[150863.611993] x2 : 0000000000038756 x1 : 0000000000000020 x0 : 0f1e328a8304a787
<7>[150863.619196] Call trace:
<7>[150863.621715] kmem_cache_alloc_node+0xbc/0x2d0
<7>[150863.626143] alloc_vmap_area+0xc8/0x8f8
<7>[150863.630053] __get_vm_area_node+0xbc/0x1b0
<7>[150863.634221] __vmalloc_node_range+0x114/0x710
<7>[150863.638647] copy_process+0x9cc/0x1408
<7>[150863.642469] kernel_clone+0x80/0x488
<7>[150863.646116] __do_sys_clone+0x5c/0x78
<7>[150863.649849] __arm64_sys_clone+0x24/0x38
<7>[150863.653843] invoke_syscall.constprop.0+0x54/0xf0
<7>[150863.658618] do_el0_svc+0x44/0xc8
<7>[150863.662006] el0_svc+0x18/0x50
<7>[150863.665134] el0t_64_sync_handler+0x118/0x128
<7>[150863.669561] el0t_64_sync+0x150/0x158
<0>[150863.673297] Code: b9402a61 f9405e65 8b010003 dac00c63 (f8616801)
<4>[150863.679457] ---[ end trace 0000000000000000 ]---
<3>[150863.695872] pstore: backend (ramoops) writing error (-28)
<0>[150863.701343] Kernel panic - not syncing: Oops: Fatal exception
<2>[150863.707156] SMP: stopping secondary CPUs
<0>[150863.711155] Kernel Offset: disabled
<0>[150863.714713] CPU features: 0x0,00000000,00000000,1000400b
<0>[150863.720094] Memory Limit: none
My performance is comparable to that of the previous 4.7.5 op firmware with the overall impression its more stable. I was advised to use the OP firmware by support because it offers superior WDS compatibility, precluding comparisons with previous versions. However, I must operate at a channel width of 40 due to the age of my home and plaster walls of the structure, which limits peak performance. Nevertheless, when within close proximity to the router, I have achieved exceptionally fast speeds when configured to a channel width of 160.
Just giving you another example that they really don't care about testing their firmwares before releasing it.
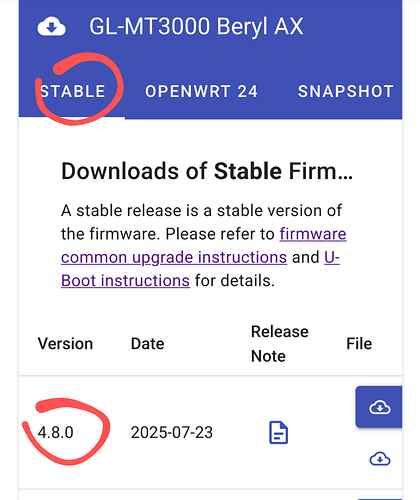
GL-MT3000 is on Stable 4.8.0 (closed source).
We reported the issue with the VPN on Beta (Op24) and the problem is also found on the Stable version.
Funny advice, but the "stable version" IS the problem! It's completely broken.
Im back to running 4.8 stable instead of op24 and do not have the Wireguard / dnsmasq issues.
Its only on op24 for me.
Im seeing nothing broken at all on any of the features i use on the v21 4.8 stable.
Admittedly i dont use or need Dyndns but im using everything else including wireguard client mode.