I had tried before in the past to do something like that on my old OpenWRT router, a combination with IPTABLES and mangle / nft, either force local traffic through WAN as normally, and then set for each IP/mac a filter which should go through tun0/vpn. And add a rule into /etc/iproute2/rt_tables 101 nonvpn for example. I couldnt get the tinyproxy to work though with something like this:
#iptables -w -t mangle -N PRX1MARK
#iptables -w -t mangle -A PRX1MARK -j MARK --set-mark 1
#iptables -w -t mangle -A PRX1MARK -j CONNMARK --save-mark
#iptables -w -t mangle -N RSTPRX1MARK
#iptables -w -t mangle -A RSTPRX1MARK -j CONNMARK --restore-mark
#iptables -w -t mangle -A OUTPUT -p TCP -m conntrack --ctstate NEW -m owner --uid-owner 1000 -j PRX1MARK
#iptables -w -t mangle -A OUTPUT -p TCP -m conntrack --ctstate ESTABLISHED,RELATED -m owner --uid-owner 1000 -j RSTPRX1MARK
###iptables -w -t mangle -A OUTPUT -m owner --uid-owner 1000 -j MARK --set-mark 1
where 1000 was tinyproxy I think.
So you say there is a filter already in the firmware, can I add other user/groups to it and then let a process like tinyproxy run under that user/group which then is forced through nonvpn?
Dont you need other packages for this to work like kmod-nft-core kmod-nft-nat and some other? what about nftable-nojson?
In my opinion the argumentation it is because of leak risk is nonsense, it is just lazy design to route everything through vpn, problem solved. You can totally do it differently for example route DNS through vpn by iptables rules for port 53 for example. First step. Then you can also do a ip/mac filtering one by one for each client, to simply say, use tun0, that would automatically also mean no traffic can leak, if tun0 is down. I would like this solution way more to have in the GLinet policy web gui, but there is no so far to add rules like this.
Interessting, so I can already do something like this:
sudo -g nonevpn traceroute 1.1.1.1
? And every command I execute this way will use WAN?
That seems to work actually:
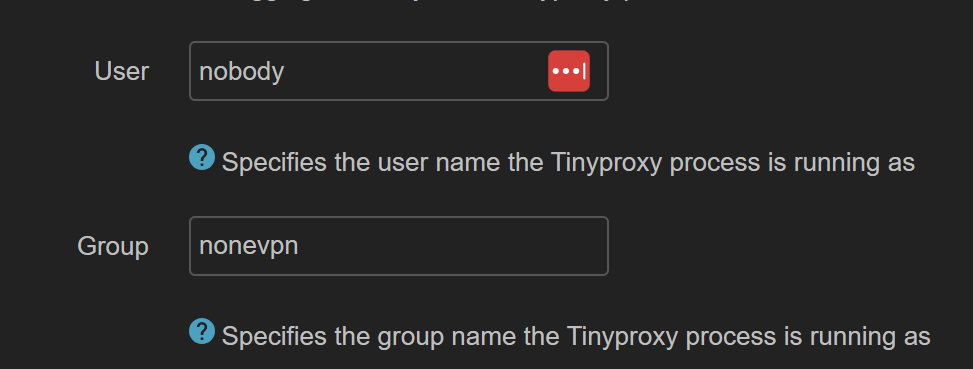
But for tinyproxy it doesnt work when I do this in luci:
I still get VPN ip when I use tinyproxy.
Update: It seems to work now. There was a glitch in the luci updating the tinyproxy.conf file and for whatever reason it didnt change the variable under /var/etc/tinyproxy.conf now after restart it seems to work.
Not sure why this feature is missing in the GLinet web gui. There should be an entire tab for this, maybe also select processes to not use VPN.