Hi All,
I got around to firing up my Flint. You cannot set the forwards through Luci (advanced) web interface on the current version as posted by contaktd:
"description": "OpenWrt Chaos Calmer 15.05.1"
There is a beta build of Flint based on openwrt 21, which does let you set the forwards as I suggested in my initial answer. I had a quick play with the beta software - worked ok for me. YMMV - its beta.
You can “probably” config it using command line/luci. You do need 2 firewall redirect rules.
Rule 1: option src ‘wan’
Rule 2: option src ‘lan’
Traffic from outside originates from the Internet, so will come in via wan. Traffic from our local PC will originate from the lan, so we need rule 2 to match this traffic.
My setup
Server: 10.101.16.200
PC: 10.101.16.173
GL Router: lan: 10.101.16.1 <->wan: 10.101.2.16 ← NAT → ISP router lan: 10.101.0.1 ← NAT → Internet.
Just noted above, so that IP addresses below are explained.
The 2 rules - both were set up in advanced web interface, on the travel version of the slate, running the version 4 beta s/w:
For the external traffic
config redirect
option src 'wan'
option name 'HTTP-Proxy-Bullseye1'
option src_dport '31887'
option target 'DNAT'
option dest_ip '10.101.16.200'
option dest 'lan'
list proto 'tcp'
option dest_port '8887'
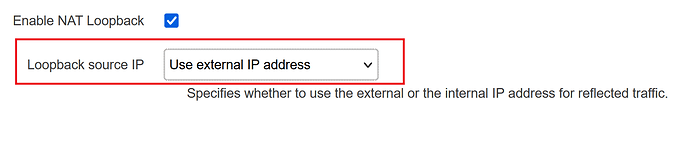
option reflection_src 'external'
For internal traffic.
config redirect
list proto 'tcp'
option src_dport '31887'
option dest_ip '10.101.16.200'
option dest_port '8887'
option src 'lan'
option name 'HTTP-Proxy-Loop-Bullseye1'
option dest 'lan'
option reflection_src 'external'
option target 'DNAT'
I point a browser on the PC to http://dns name:31887/page.html
This above gives following conversation when I visit the page in the browser. External IP address hidden as external ip.
root@GL-AXT1800:~# tcpdump -nnn -i br-lan tcp port 31887 or tcp port 8887
tcpdump: verbose output suppressed, use -v or -vv for full protocol decode
listening on br-lan, link-type EN10MB (Ethernet), capture size 262144 bytes
21:41:26.296043 IP 10.101.16.173.18285 > external_ip.31887: Flags [S], seq 1355366318, win 64240, options [mss 1460,nop,wscale 8,nop,nop,sackOK], length 0
21:41:26.296316 IP 10.101.2.16.18285 > 10.101.16.200.8887: Flags [S], seq 1355366318, win 64240, options [mss 1460,nop,wscale 8,nop,nop,sackOK], length 0
21:41:26.298030 IP 10.101.16.200.8887 > 10.101.2.16.18285: Flags [S.], seq 707098590, ack 1355366319, win 64240, options [mss 1460,nop,nop,sackOK,nop,wscale 7], length 0
21:41:26.298159 IP external_ip.31887 > 10.101.16.173.18285: Flags [S.], seq 707098590, ack 1355366319, win 64240, options [mss 1460,nop,nop,sackOK,nop,wscale 7], length 0
21:41:26.301028 IP 10.101.16.173.18285 > external_ip.31887: Flags [.], ack 1, win 513, length 0
21:41:26.301265 IP 10.101.2.16.18285 > 10.101.16.200.8887: Flags [.], ack 1, win 513, length 0
There was more data, but the 3-way handshake above should demonstrate the rules working.
Hope this helps.
Simon