Okay lets start from the basics then.
So I go make two tutorials one with a wired port and one as routed ap.
Because maybe vlans are not the right terminology for this use case, what you look for is a routed ap.
For Vlan:
click here to open
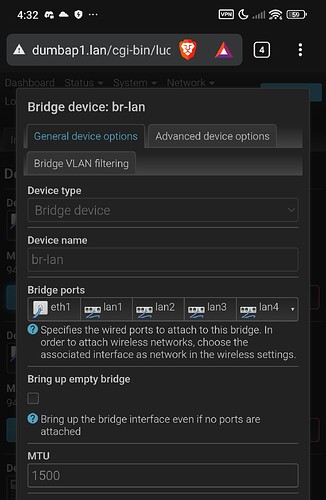
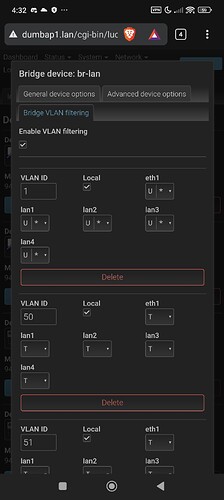
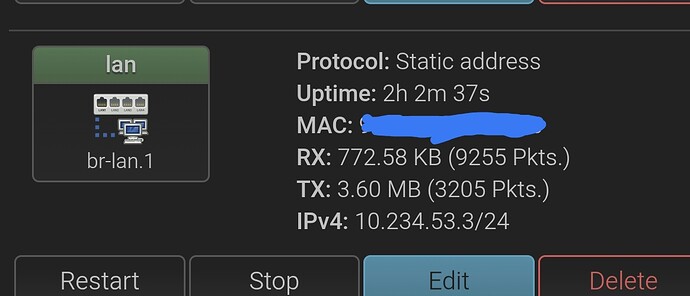
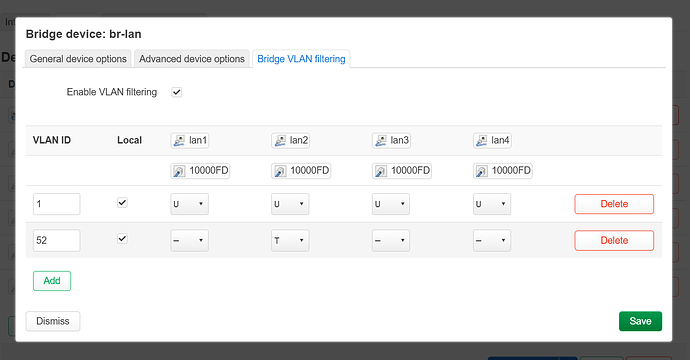
First lets make vlan50, in this tutorial we assume br-lan.1 already has been assigned to interface lan, if not please edit the lan interface with br-lan.1 or you will not have lan connectivity.
note that we choose to use vlan 50 on port 2, if your situation is different and only require wireless and not a mix between wired maybe vlan isn't the right terminology in that case you could better call this a routed ap.
U means untagged, untagged vlans do not traverse further, basicly there can only one per port and often is the default vlan, or better said the final destination port.
T means tagged, tagged vlans can traverse further meaning that a other vlan aware device can use them towards the destinated port like a switch which then untags it.
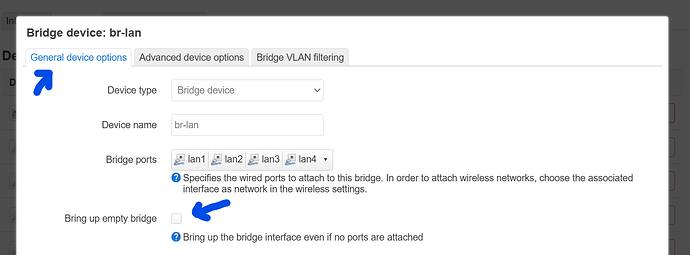
To continue we also have to check this checkbox this is to make sure even if no lan port is active the wifi can hook into the bridge because the bridge keeps alive:
now navigate to:
scroll down and click on here:

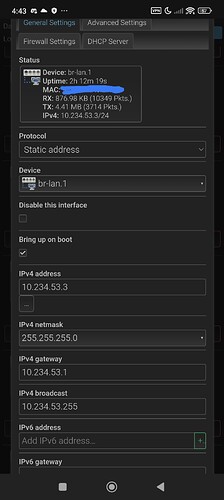
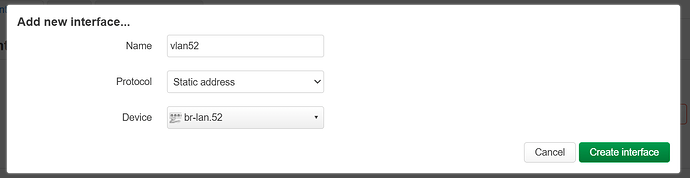
then we fill in:
now you see this:
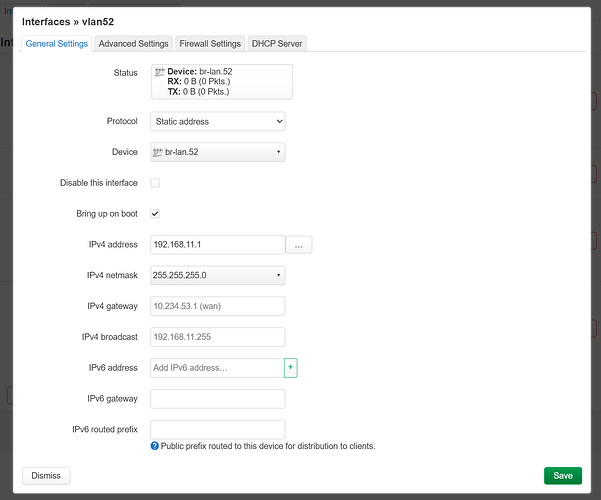
you want to fill it in like this:
note that the ip can be everything, there is a table on the internet called rfc1918 search for it,it can also be 192.168.12.1 for that mather max 254
please look very carefully to the colors of the text, gateway for example is blank (this is auto filled in by openwrt just leave it as is).
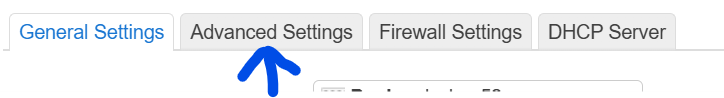
now lets navigate to:
and uncheck this:

this means that OpenWrt doesn't see this interface as a gateway type interface like wwan/wan you don't want this conflict 
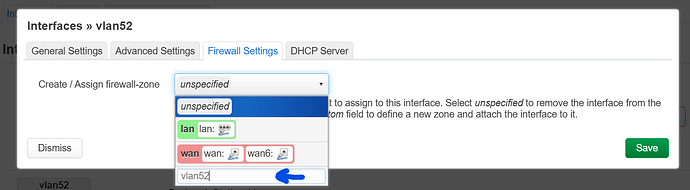
now click here and fill and press enter:
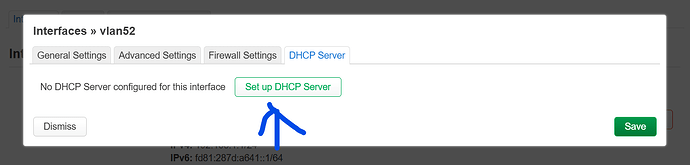
now click on dhcp server and create one:
and now you click on save, then you scroll down and click on save and apply.
great now the network has been set, but the firewall needs some tweaking lets go to the firewall.
luci->network->firewall
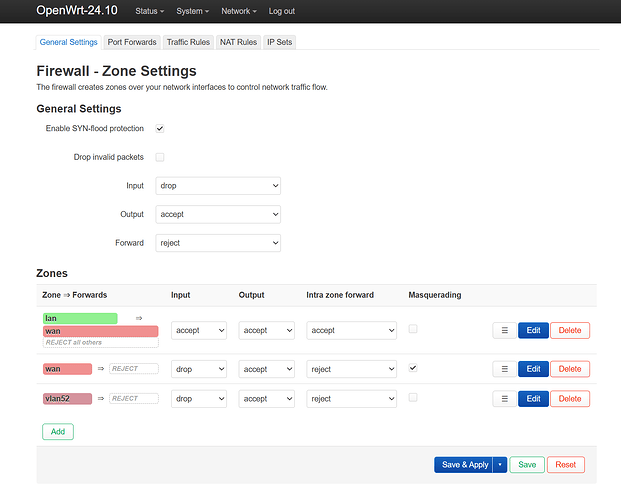
it will look close to this:
and you want to change this:

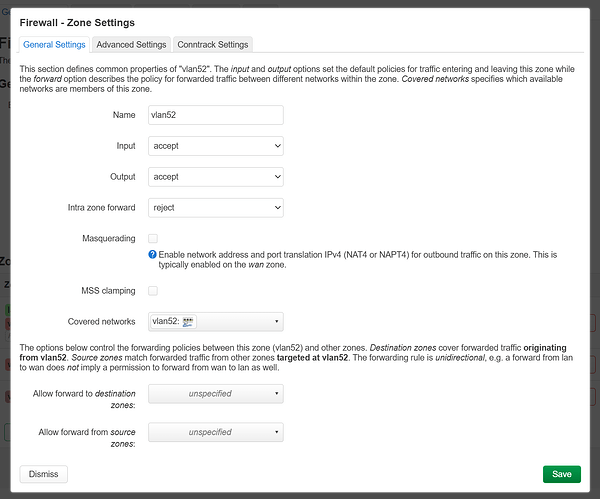
to:

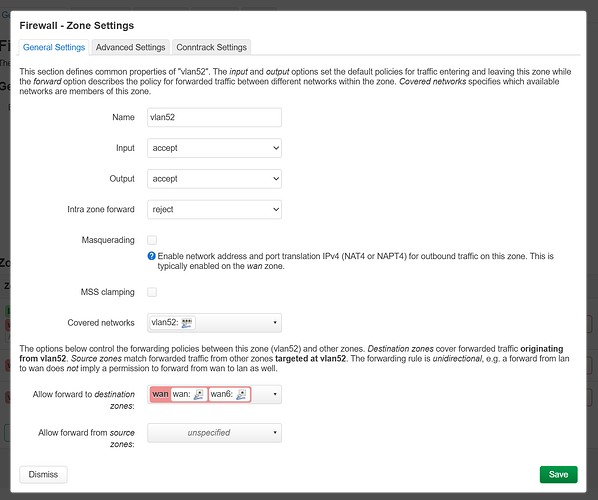
click save and apply, then edit vlan52.
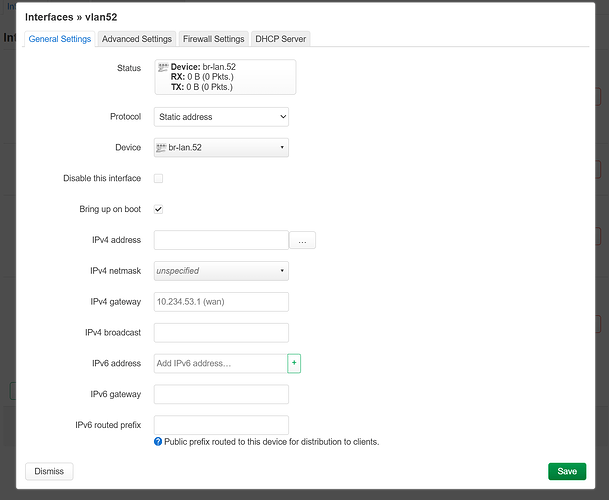
you will see this:
and you want to change it to this:
great!, now we got the networking done, dhcp working, and the firewall allows dhcp requests, now we only need to fix wifi, unfortunately this was on proxmox so I had to take my original router as example.
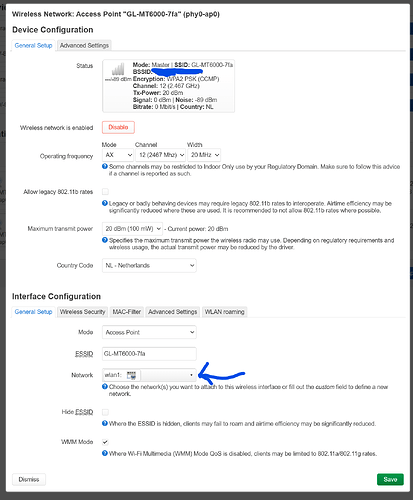
you go to luci->network->wireless, edit the band or add one, adding is not that super special you can look to existing wifi networks to make a example and re-create it.
you will see something like this, please click on network and select vlan52:
please note it is important to use lowercase, linux is very case sensitive thus it is better to make interface namings lowercase 
For RoutedAP:
click here to open
For a routed AP it's alot easier, basicly you only want to create a empty bridge where the wireless phy interface hooks on in where it becomes a working device for a interface.
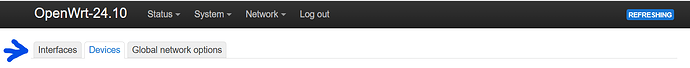
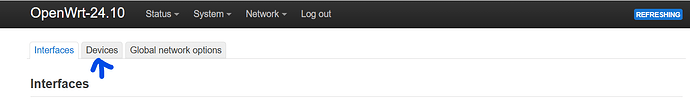
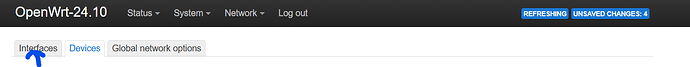
please navigate to luci->network->interfaces.
Then click on the devices tab like here:
then scroll down and click on

Then click on here:
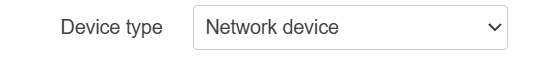
and select Bridge device.
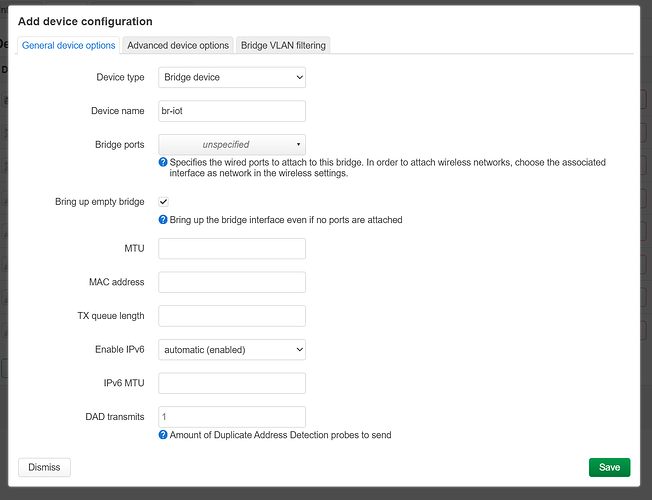
please fill it in like this:
and check the Bring up empty bridge, otherwise issues will happen  , click save.
, click save.
Now click back on interfaces:
scroll down and add a interface, note we call things vlan here but don't let you get confused here I just copied half from the first tutorial, so just name it something else than vlan  , this has nothing to do with vlans
, this has nothing to do with vlans 
scroll down and click on here:

then we fill in:
^ note: br-lan.52 doesn't exist, of course we need to use br-iot thats the only difference.
now you see this:
you want to fill it in like this (yes again, you use br-iot):
note that the ip can be everything, there is a table on the internet called rfc1918 search for it,it can also be 192.168.12.1 for that mather max 254
please look very carefully to the colors of the text, gateway for example is blank (this is auto filled in by openwrt just leave it as is).
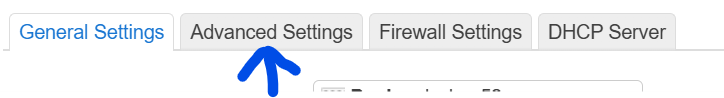
now lets navigate to:
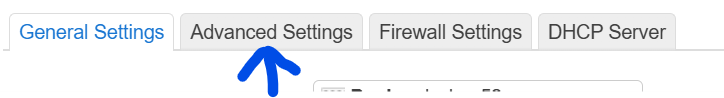
and uncheck this:

this means that OpenWrt doesn't see this interface as a gateway type interface like wwan/wan you don't want this conflict 
now click here and fill and press enter:
now click on dhcp server and create one:
and now you click on save, then you scroll down and click on save and apply.
great now the network has been set, but the firewall needs some tweaking lets go to the firewall.
luci->network->firewall
it will look close to this:
and you want to change this:

to:

click save and apply, then edit vlan52.
you will see this:
and you want to change it to this:
great!, now we got the networking done, dhcp working, and the firewall allows dhcp requests, now we only need to fix wifi, unfortunately this was on proxmox so I had to take my original router as example.
you go to luci->network->wireless, edit the band or add one, adding is not that super special you can look to existing wifi networks to make a example and re-create it.
you will see something like this, please click on network and select vlan52:
please note it is important to use lowercase, linux is very case sensitive thus it is better to make interface namings lowercase 
There are a few issues to note about gl firmware:
- the clients menu doesn't work for custom interfaces it listens to (lan,guest).
- vpn policies may have incompatibilities.
^ some of these things will be fixed at a later time.