Hi All
Despite trying plenty of vids, self-help, guides and the like, I’m no better off trying to resolve this.
I have an MT6000 Flint 2 (on stock Firmware V4.8.3 & OpenWrt 21.02-SNAPSHOT) with a LAN connection to TP-Link Archer BE400 (LAN to LAN) in AP Mode in another Room.
Flint 2:
Main Wi-Fi Network, 2.4 & 5GHz both SSIDs, called ‘DivLAN', with same password.
Guest Network Enabled for both 2.4 & 5GHz bands, with SSID of 'DivGuest', with same password.
Archer In (AP Mode):
PC is connected to LAN port on Archer and other ports are for other devices.
WiFi network SSIDs and passwords are replicated from Flint 2.
I want to create an IoT network on the Flint 2 for one or more Wi-Fi cameras. Apart from isolation and dialling home to ‘whoever’ paranoia, the cameras have to be entirely reset if there’s a change of SSID or Password, losing all settings which is a right PITA.
- Camera will need to be controllable from devices on main ‘DivLAN’ WiFi
- Camera Needs WAN access to provide remote access via it’s cloud server via my mobile phone when I’m out and about.
- Camera should have no LAN Access.
Issues:
- Presently, Archer in AP mode just feeds everything back to Flint 2 via LAN connection for the Wi-Fi networks (DivLAN’ & ‘DivGuest’, so there’s obviously no segregation or isolation with devices just getting an IP from the DHCP Flint 2 - total waste of time. This is before even attempting to setup IoT.
- It seems impossible to create a simple IoT network on the Flint 2 via GL GUI - it needs Luci. I have tried for weeks to do this without success, creating the interface, DHCP, Firewall etc. I’ve exhausted AI with this to the point my blood pressure was going through the roof dealing with the likes of Chat GPT et al. I have several scripts and then scripts to correct scripts from GL Support without success. Often router is left inaccessible after rebooting, requiring reflashing again to stock. It fails each time or I have total loss of WiFI on router.
- As it now stands Support have suggested I should probably wait for V4.9x of the Firmware which is supposed to include native IoT support in the GL GUI!
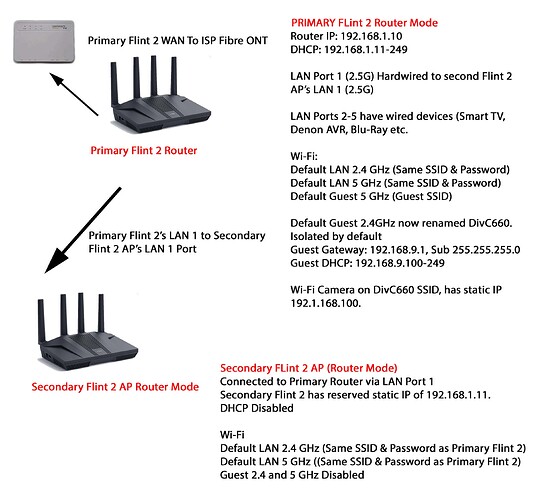
As for the Archer AP, I am now deciding whether to purchase a second Flint 2 and use that in AP mode as it can replicate existing WiFi networks from the Main Flint 2 and maintains the Segregation (but will likely require setting up again via Luci). Given the initial problems with even attempting this on the main Flint 2 without success is not encouraging.
I've just about given up attempting this with AI help as all that does is screw things up and results in a firmware reflash being required! Also, it's pretty useless as it gives incorrect versions of syntax for later versions of OpenWRT which don't work.
So I don't know whether it's worth investing in another Flint 2 if it's just going to be too complicated to set up and to be honest. A PHD in rocket science should not be something that consumers are required to have in order to set up a basic IoT network and then replicate segregation on another AP.
Why is this basic functionality really so awkward to do?
I don’t think what I’m attempting to achieve is unreasonable, considering the very complicated projects that some people have undertaken. If anyone has any pointers, or has done this, perhaps they could chip in or better still send a script that I could amend as needed.
TIA